Malicious actors can replace cryptocurrency addresses thanks to this clipboard malware
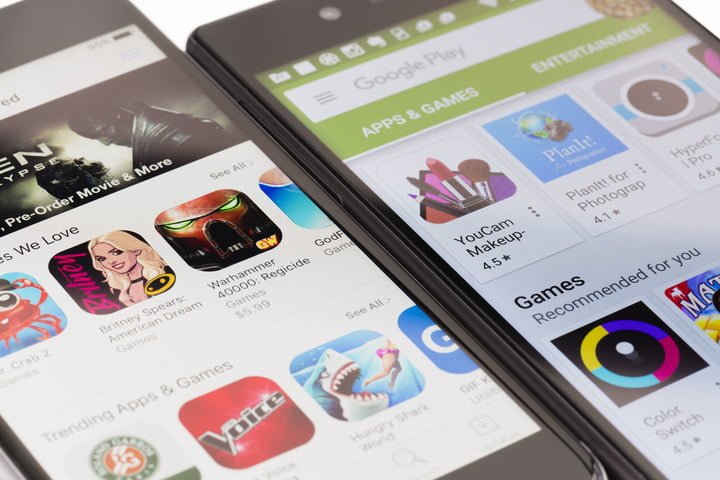
Network security and ethical hacking specialists from the International Institute of Cyber Security report a new malware-related incident in Google Play Store. According to reports, a new malware variant used to replace the contents of the clipboard of an Android device (this variant is known as clipper malware) has been found in the Google apps store platform.
This kind of malware was first reported in 2017, infecting some Windows devices, while in 2018 it was detected in an unofficial Android apps store. This 2019, the clipper malware finally arrived to the Play Store platform.
The malware was present in a malicious app and the main goal of its developers was to collect the access credentials and passwords of the victim’s computer to steal virtual assets. This malware is also capable of stealing an online wallet address from Bitcoin or Ethereum on the replacing it victim’s clipboard with addresses known to the attacker.
Malware, dubbed Android/Clipper.C by network security experts takes advantage of the way a user enters a Criptomoneda address. Because these addresses are composed of long random character strings, users prefer to copy and paste addresses using the clipboard instead of entering each symbol manually. It is at this point where the malware replaces the victim’s address with another one in possession of the hacker.
The researchers found this malware in the MetaMask app, a plugin that allows Ethereum users to perform transactions through conventional websites. This plugin is available for Firefox and Chrome, but the company does not have mobile applications for any operating system, which means that the attackers created a fake app from the company to achieve their goals.
The fake MetaMask app has already been removed from Play Store, although experts in network security do not rule out the possibility that variants of this malicious software are present in other applications available in the Google app store.
When analyzing the cryptocurrency addresses associated with this malware, it was discovered that the attackers have extracted 0.12868189 Bitcoin ($460 USD) and 0.00909752827411204 Ethereum (just equivalent to $1. 05 USD).
Cybersecurity experts recommend Android users, especially those who use this kind of virtual assets, be careful with these malicious developments, it is highly probable their presence in other applications.
Before downloading a Play Store app, the user should take a look at the developer’s website, because there you can find the link to the official app. If it is not possible for the user to corroborate the authenticity of the software, it is recommended not to download/install the application.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











