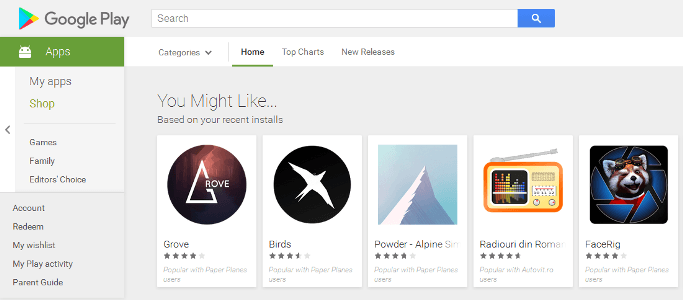
This advertising software is located in 210 Android apps available in the official Google Play store
A figure close to 150 million of Android device users could have downloaded and installed an application that includes a new variety of an adware known as SIMBAD, reported network security and ethical hacking specialists from the International Institute of Cyber Security.
According to reports, adware is hidden as an advertising kit (RXDrioder), used by all affected applications to control how ads are displayed to users.
Subsequent reports from a network security firm claim that RXDrioder developers have been using this kit’s code to hide the malware in some applications for the purpose of hijacking infected devices and displaying ads for their own benefit.
“We theorize that developers were tricked into installing this malicious kit, oblivious to its development”, the experts mentioned. In total, the company identified the malicious advertising kit within 210 Android apps available through the official Google Playplatform (mainly videogames). In total, the compromised applications have been downloaded by 150 million users.
Network security experts commented that the kit contains multiple hidden features that have nothing to do with this kind of tool. According to reports, RXDrioder can hide the icon of an application (a trick used by multiple malicious apps), among other features, although researchers consider that software was abused primarily for advertising use.
SIMBAD operators are even able to send instructions to the applications that integrate RXDroider to take control over these without legitimate developers discovering it.
Although experts believe that the abuse of the app was for publicity, they believe that operators could also have forced the browser to enter a URL and show even more publicity or even enter Google Play and download specific applications.
Shortly after the publication of these reports, all applications using the RXDrioder tool were removed from the official Google Play platform. This adware campaign binds to past incidents with other adware variants, such as Chamois, HummingBad and Googligan.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











