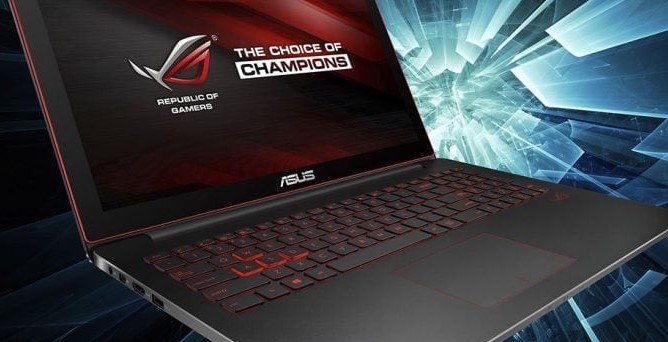
According to the authors of the book ‘Learn ethical hacking’, a group of hackers has infected hundreds of thousands of Asus computers using the company’s own update tool. According to specialists from the International Institute of Cyber Security, Asus, a company based in Taiwan, is one of the leading companies supplying portable computer equipment worldwide.
The attack was detected in January, after the hacker group took control over the Asus Live Update Utility tool to install malware on the victim’s devices without the company noticing; in the end, multiple cybersecurity specialized media began to resume information.
This campaign, nicknamed ‘Operation ShadowHammer’ by the authors of ‘Learn ethical hacking’, was carried out between July and November 2018; the first investigations found that around 60k users of Asus products had been infected.
However, the authors of ‘Learn ethical hacking’ highlighted that the campaign of infection could have affected more than one million users of Asus. Live Update Utility is a pre-installed tool for most of Asus newest products.
According to the investigation, the hackers managed to infect the compromised machines without the malware detection systems being activated, since the reliable security certificate of Asus was used, same that it is hosted on the servers of the company.
This incident has generated new concerns for technology users, as it will always be worth asking if the updates delivered directly by technology vendors are reliable. Moreover, this kind of attack is not something new; according to the experts of the IICS, a couple of years ago a group of threat actors hijacked the popular tool CCleaner to install malware in millions of devices.
As if it was not enough, the little confidence users have in automatic updates could also be advantageous to malicious hackers. For example, most of the computers infected with WannaCry ransomware were easily compromised because a routine security update was not installed.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











