BasBanke is a new variant of malware for Android mainly directed to users of this operating system in Brazil. According to the authors of ‘Learn ethical hacking‘, it is a banking Trojan that steals sensitive financial data, such as card numbers, card type, etc.
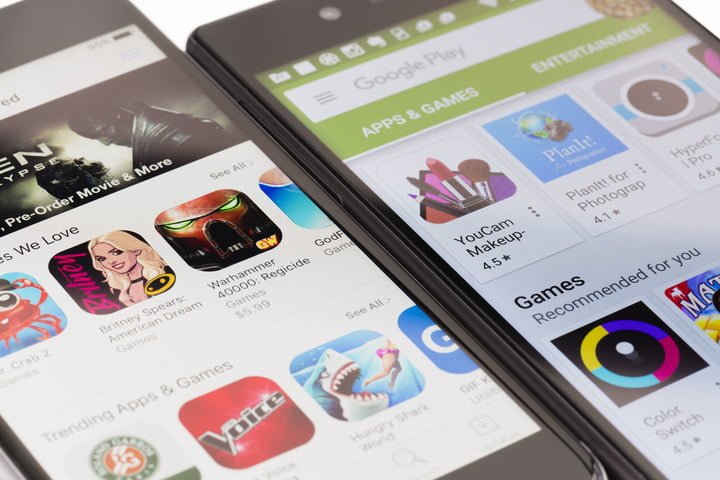
According to the authors of ‘Learn ethical hacking’, the propagation of this threat began during the electoral process in Brazil, after several apps were downloaded and installed around 10k times from the official platform of Google Play.
This malware can perform tasks such as logging keystrokes, screen recording, stealing SMS messages and financial information and payment card details. To deceive users and get them to download malware, threat actors are advertised through social media platforms, as well as forwarded messages in WhatsApp. Once the user is deceived, the attackers redirect it either to a malicious website, or to the official Google Play platform.
Malicious applications hosted on Google Play Store are disguised as legitimate applications, such as QR readers, non-existent travel agency apps and others that offer various services for Android, such as the fake version of CleanDroid. This malicious development promises antivirus protection, storage optimization, etc; the banking Trojan is hidden in any of these apps.
According to the authors of ‘Learn ethical hacking’, the number of fake apps and malicious sites is really considerable. Multiple Brazilian financial institutions, and online services like Spotify, Netflix, YouTube, are among the most used for the attack. However, when it comes to stealing bank credentials, metadata such as the device name, the IMEI and the phone number used by the victim are sent to a remote C2. According to specialists in cybersecurity, threat actors use all this information to gain access to the victim’s accounts in the most discreet way possible.
Similar Campaigns have appeared before, however, the specialists consider that BasBanke is especially damaging because of the channels of diffusion that it uses to reach the victims (Facebook and WhatsApp mainly). Also, this campaign is a new example of how relatively easy it is to place a malicious app in the official Google store.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











