Everyone would have well known with capturing network packets using analyzer tools. But very few have known with capturing with USB packets. We are talking about USB sniffer which is quite often used in ethical hacking courses offered by International Institute of Cyber Security . USB sniffers capture and shows the packets which are transferring.
USB Protocols :-
USB interface consists of layers of protocol. In USB interface lower level layers are single handled. USB packets contain information like :-
- Data exchange
- Controlling the Data exchange
- Error correction & detection
USB contains Different packet fields :-
- SYNC – It is important field holding at start of the packet. For low and full speed mode, this field is 8 byte long and 32 byte high.
- PID – Indicates packet id. it shows that what type of packet is being sent. This field is 8 bit long.
- ADDR – This field stores the destination address of USB device.
- CRC – Cycle Redundancy Check is used to check for any error in the data packet.
- EOP – End Of Packet Signals the data lines for single-ended zero.
There are two methods to capture USB packets – GUI mode using Wireshark and the CUI mode using USBPcap installer.
- We will test wireshark on Windows 10 with build version 1709.
- Download Wireshark from : https://2.na.dl.wireshark.org/win64/Wireshark-win64-3.0.2.exe
- Install the wireshark. Make sure to install USBPcap while installing wirehark. If USBPcap does not install, go to : https://github.com/desowin/usbpcap/releases/download/1.2.0.3/USBPcapSetup-1.2.0.3.exe
- Install the USBPcap. After installing Wireshark & USBPcap. Start the Wireshark.
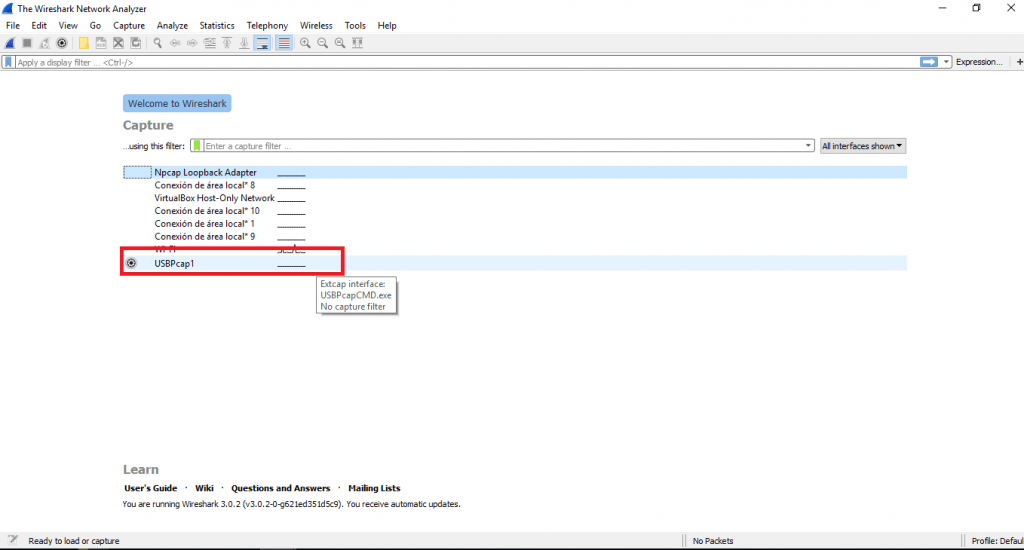
- Click on USBPcap1 & then connect USB device. And then start copying data from local computer to connected USB device.
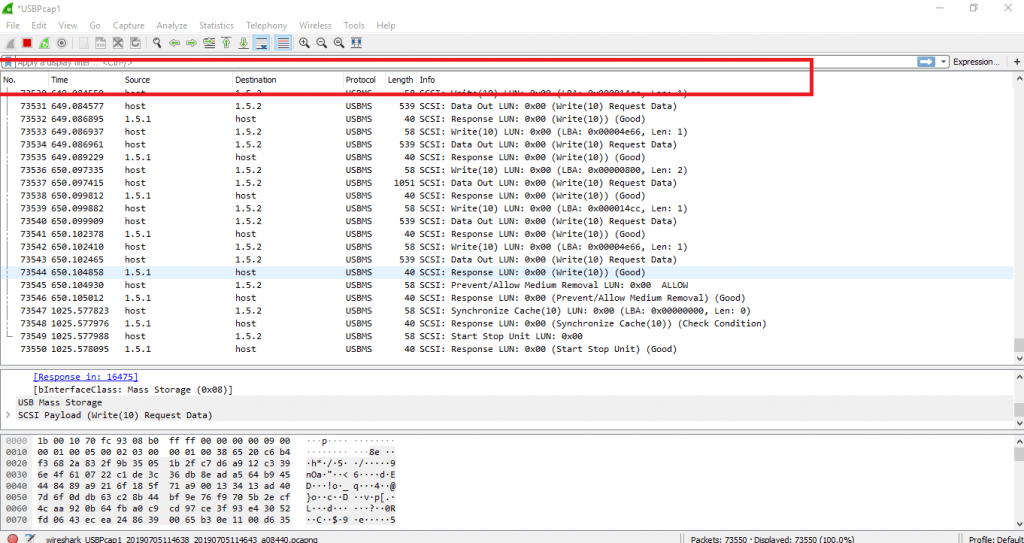
- As you will start the copying the data. You will see the packets transferring from source to destination in wireshark.
- Above screenshot shows packets transferring from host to destination. The data is transferring on USB Mass Storage. Then it data is being transferred using protocol USBMS.
- The USB mass storage is an computing protocol determined by USB implement Forum. USBMS makes USB device accessible to host. USB device works as external Hard drive.
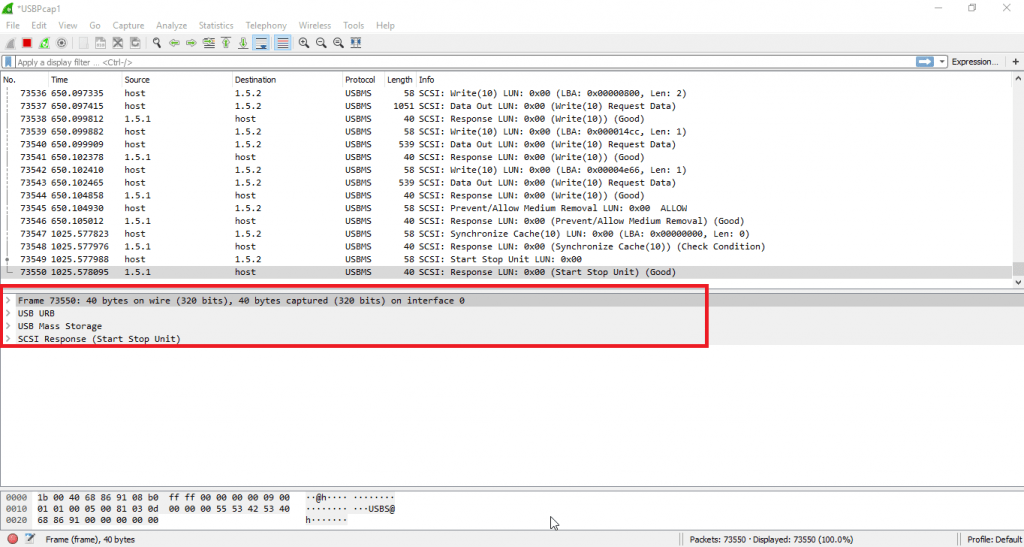
- Now we will analyze data packet. And we will try to explain each & every information which shows.
- Firstly it shows the frame. Frame is consisting basic info of the transferring bytes.
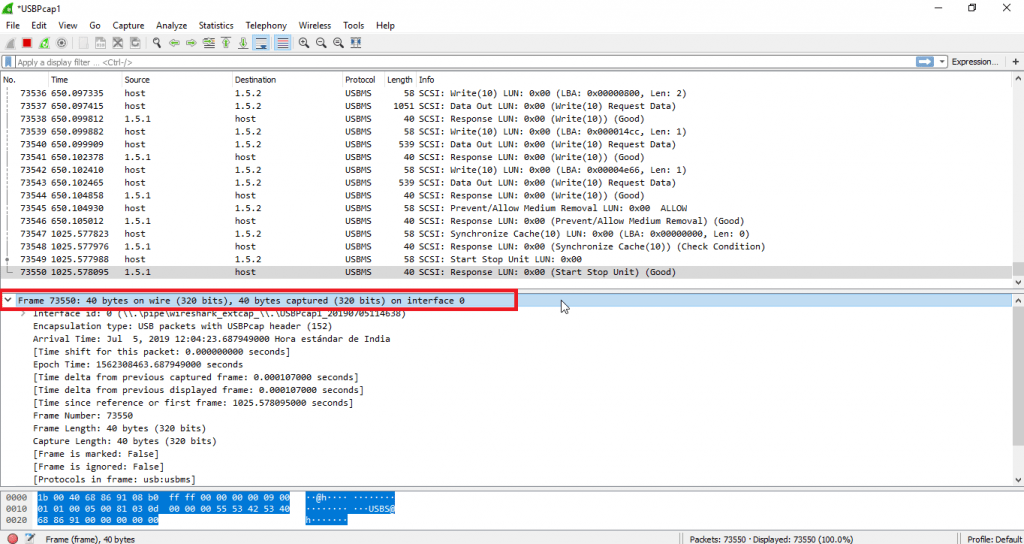
- Above screenshot shows the details about Frame of 40 bytes. Then it shows the interface ID on which data is captured.
- Then frame is having info of frame length, frame number & bytes. Then it shows complete time details from previous captured & displayed frame. All this analysis is part of ethical hacking course run by International Institute of Cyber Security.
- Further details it shows USB URB information which consists of IRP ID and IRP info.
- There are other light weight packets analyzer like termshark available on internet.

Cyber Security Researcher. Information security specialist, currently working as risk infrastructure specialist & investigator. He is a cyber-security researcher with over 25 years of experience. He has served with the Intelligence Agency as a Senior Intelligence Officer. He has also worked with Google and Citrix in development of cyber security solutions. He has aided the government and many federal agencies in thwarting many cyber crimes. He has been writing for us in his free time since last 5 years.