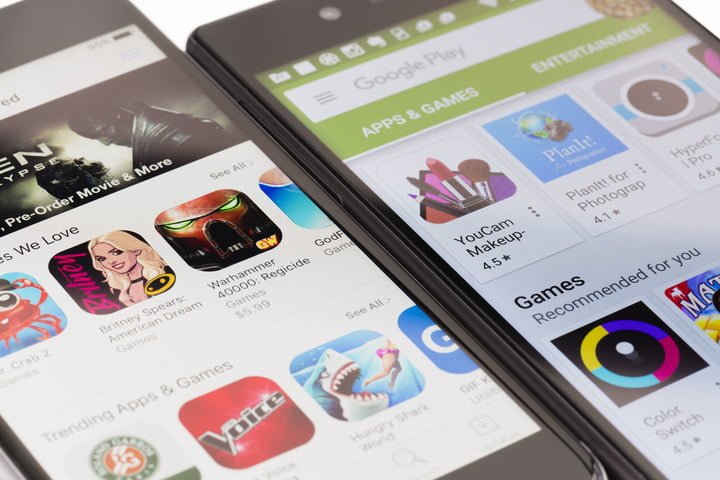
Security flaws in dozens, or even hundreds, of Android apps available on the Play Store platform remain a serious inconvenience for Google, app developers and especially users. According to vulnerability testing specialists, the company is set to update its bounty program, known as the Google Play Security Reward Program (GPSRP), hoping to reduce security risks for smartphone users.
The most important modification this program has undergone is that researchers will now be able to aspire to get a bounty for reporting security vulnerabilities in applications developed by third parties outside Google.
“The scope of our bug bounty program will increase, as it now includes all apps available on the Google Play Store that have at least 100 million downloads,” says Patrick Mutchler, a vulnerability testing expert at Google. “Researchers will be able to get bounties for their reports regardless of whether the developers of vulnerable apps have or not a vulnerability bounty program,” he added.
Under Google’s new security standards, if a vulnerability testing expert discovers a security flaw in an application that meets the requirements mentioned above, Google will serve as a responsible disclosure platform for the notifying developers and giving the reward to researchers. On the other hand, if the developers of the vulnerable applications have a bug disclosure program, they will be able to aspire to collect the reward granted by the developers, as Google will provide a bonus for the report.
The main beneficiaries of this decision are independent security researchers, as they are being offered an easy way to get a payment for their work; in addition, developers of popular apps but without enough resources to set a bug bounty program will also experience the benefits of Google’s new policy.
In addition to this announcement, Google made some minimal changes to the requirements that a report must meet in order to get a bounty, specifying what kind of security flaws are involved in the GPSRP program:
- Remote Code Execution (RCE) vulnerabilities: Researchers should demonstrate that it is possible to run native ARM code on the victim’s device without their approval or knowledge. This kind of reports could be awarded with up to $20k USD
- Theft or exposure of sensitive data: It refers to the unauthorized access to the victim’s personal information stored on their mobile device. To get the bounty, the researcher must verify that it is possible to extract information from an Android device with factory security settings enabled. Google grants up to $3k USD for these flaws
- Access to protected app components: This flaw occurs when one of the components of an app processes a previous Intent from another app without validating it correctly, causing the targeted app to perform an operation for which the sending app does not have permissions. These flaws are also rewarded with $3k USD by Google
Specialists in vulnerability testing services from the International Institute of Cyber Security (IICS) believe that by expanding this program Google is also trying to involve developers in their vulnerability disclosure method rather than publicly releasing the flaws without notifying affected developers, as this practice could be beneficial for threat actors.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











