Ransomware remains one of the most practiced cyberattack variants and generates great stakes for threat actors, mentioned digital forensics specialists. Although organizations or individuals who are victims of these infections often have appropriate security measures, a slight oversight is sufficient to let the malware into the target system.
In addition, a ransomware infection can be disastrous, as the victim might not have backups of the encrypted information, which would force them to negotiate with the attackers, although there is no guarantee that the criminals will comply with their share of the deal and restore the access to information.
Fortunately, multiple independent researchers and digital forensics firms have thoroughly analyzed the known variants of encryption malware, even succeeding in developing tools to remove the encryption imposed by some variants of ransomware. Below are three free alternatives to remove the encryption of three popular ransomware variants: FortuneCrypt, WannaCryFake and Yatron.
Yatron
A few years ago, a researcher released the code for Hidden Tear, a popular encryption malware, for educational outreach purposes. However, the material came into the hands of threat actors, who used it to create other malware variants, such as Yatron. Due to some failures in the development of this malware, Kaspersky Lab specialists managed to create a tool to recover files encrypted with Yatron.
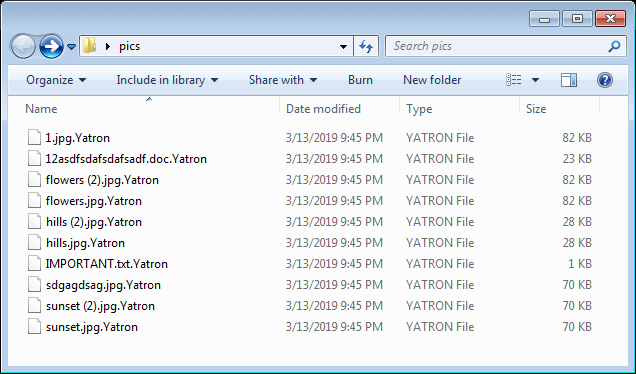
YATRON DECRYPTOR-DOWNLOAD HERE
FortuneCrypt
Soon after, the tool to remove the encryption of FortuneCrypt, a ransomware variant that caught the attention of the cybersecurity community, was also revealed as it was written in Blitz BASIC, a programming language designed to attract the novice programmers. This ransomware used a weak encryption routine to block access to victims’ information, which facilitated the creation of this tool.
FORTUNECRYPT DECRYPTOR-DOWNLOAD HERE
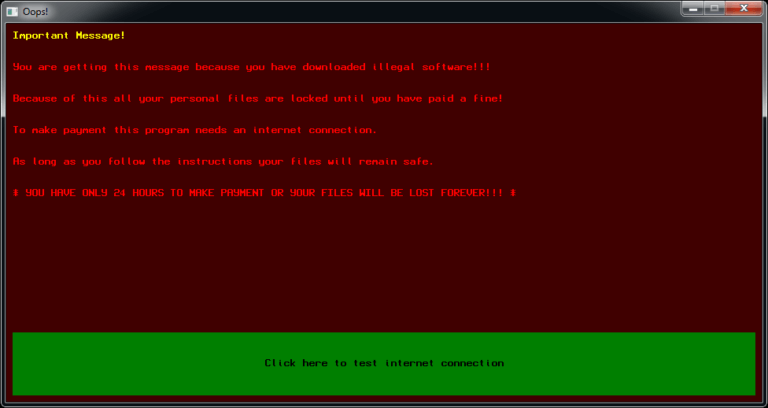
WannaCryFake
Specialists from the firm Emsisoft have released a free tool to remove the encryption imposed by the WannaCryFake ransomware variant. As reported, this is a variant of ransomware that uses AES-256 to encrypt the files on the target system, adding the .WannaCry extension. In the ransom note that Victims of WannaCryFake receive, they are demanded not to attempt to remove encryption with third-party software, as this could cause permanent data loss. However, experts claim that this tool can help recover encrypted information without putting it at risk of loss.
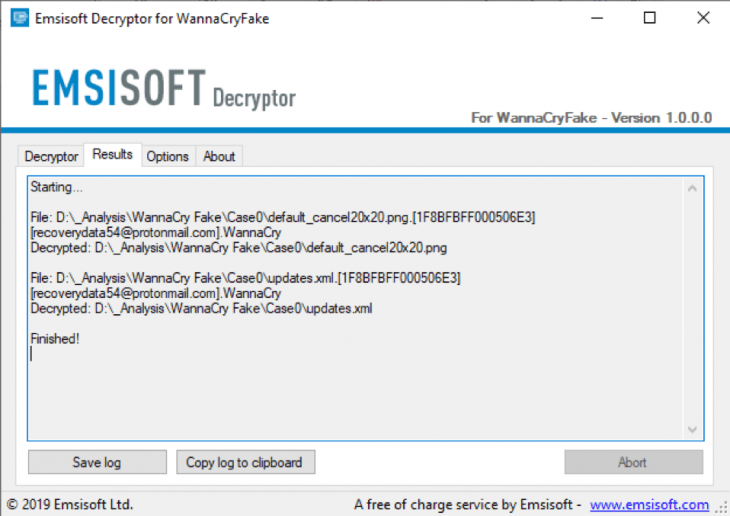
WANNACRYFAKE DECRYPTOR-DOWNLOAD HERE
International Institute of Cyber Security (IICS) digital forensics specialists mention that hackers typically resort to two methods to develop ransomware variants: reconfiguring an existing variant or creating a completely new strain. It’s really complex to stay on top of the new ransomware variants that pop up from time to time, so it’s important to take advantage of the tools to combat some of these variants.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











