China could be home to one of the biggest hacking scandals that have occurred recently. Reports from ethical hacking experts claim that this operation involves senior Chinese government officials, malicious hackers, security researchers and even insiders in multiple companies around the world.
According to reports, China mounted this hacking operation to inadvertently extract intellectual property vital to reduce the technological breach in the aviation field between the Asian giant and the most developed countries in that regard. The hacking operation also involves Comac, a Chinese government-controlled aerospace company, and the construction of C919, its most advanced aircraft, designed to compete with leading companies such as Airbus and Boeing.
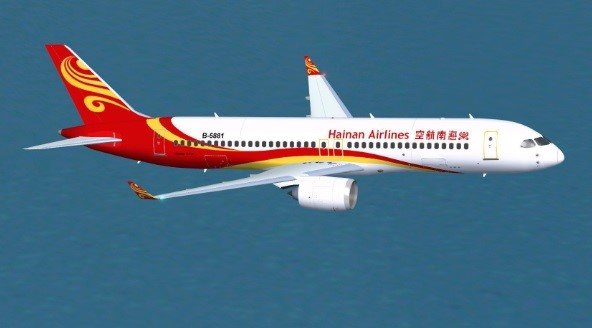
In the report, Cloudstrike ethical hacking specialists say the Ministry of State Security coordinated a systematic tracking campaign targeting some foreign companies, including some component and technology suppliers for the C919 aircraft with the aim of developing all parts of this aircraft in China in the near future.
The ministry would have commissioned its division in Jiangsu to deploy this campaign. In turn, Jiangsu delegated to two officials the coordination of attacks against private companies. The tasks of these coordinators included overseeing hacking activities, recruiting required personnel, and establishing lines of action.
It is estimated that the campaign remained active for at least 5 years, time during which hackers, identified as Turbine Panda, managed to infiltrate multiple companies, mainly providers of technology applied to aviation, such as Ametek, Honeywell, Capstone Turbine, among others.
Another feature to note is the integration of the hacker team in charge of this campaign. Ethical hacking experts say that a specialized area of the Chinese military is often in charge of this kind of activity. However, this time China decided to recruit various clandestine hackers and independent security researchers. The primary task of these hackers was to find a way to access the networks of the target companies, employing dangerous malware variants such as PlugX, Winnti or Sakula, as well as collecting sensitive information and sending it to remote servers.
While this campaign seemed to be running smoothly for the Chinese government, the hackers made a big mistake when trying to incorporate insiders from larger targets, such as Airbus and Boeing. These intrusion attempts didn’t go unnoticed for US intelligence agencies, which began gathering clues to shut down the operation.
The first to fall were employees of the attacked companies that acted as insiders for Turbine Panda. The US later managed to arrest the hacker known as Yu, developer of the Sakula malware.
The arrest of this hacker generated a strong response from the Chinese government, which prohibited its researchers and ethical hacking experts from participating in any conference or event organized abroad. However, this measure could also be interpreted as a defensive move with which China hopes to keep some of its assets away from occidental authorities.
Experts from the International Institute of Cyber Security (IICS) mention that the biggest coup to Turbine Panda came in late 2018, when Xu Yanjun, a senior Chinese official, was arrested in the occident. This is considered to be the arrest of a major foreign officer since the Cold War era. The authorities expect Yanjun to cooperate in exchange for a reduction in his conviction.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











