For different reasons, many times we have wanted to delete internet presence or remove everything the Internet knows about us. Whether there are too many bad memories, embarrassing photos or for privacy reasons, cyber security experts always come across the question: “Can I erase any trace of mine from the network?
The good news is that this is really possible to delete internet presence; there is even more than one way, although it is not a simple process. Through Twitter, the user @somenerdliam issued a series of recommendations to erase the trail we leave online. Before you begin, you need to review, if possible, any email account you have used for the past 10 years.
It will start by searching each email account for any newsletter in which you have subscribed, as these services have access to your data, information security specialists say.
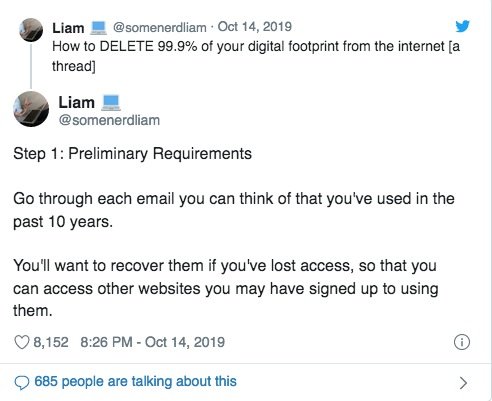
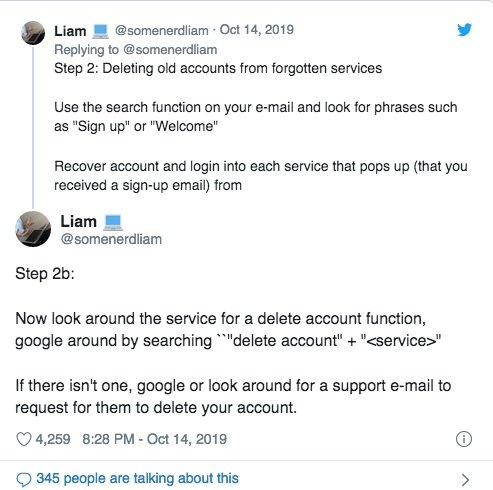
In your email service, you can search for any phrase such as “welcome”, or “Register”. Once there, you can recover the accounts and log in to each forgotten service, so you can delete the subscription by choosing that feature, or by requesting the deletion of your data from the responsible company.
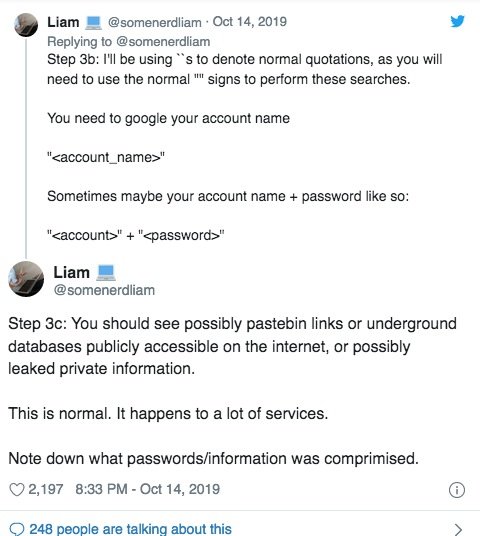
Some of these services must also delete any messages or posts before deleting the account, as a copy could be stored by a hacker or company. In addition, you should verify your information has been embroiled in some data breach incident. A good way to find out if our data has been exposed is to use the haveibeenpwned.com platform, where anyone can log in their email account and check if this information has been part of any known data breach. This will help you delete internet presence.
Deleting our data from Google is an essential part of this process. The best way for Google to forget about our existence is to ask the company to delete our records of results in Google search, although this will take months. cyber security experts at the International Institute of Cyber Security (IICS) add that it would be desirable to restrict access and Google to your data. In the Activity Controls option of your Google Account, you can customize the type of tracking your company can make of your information.
Once we restrict Google tracking and delete unused services, we can delete our old email accounts. Any inactive or unnecessary account must be closed. Adopting new security measures, such as regular password reset, will help us consolidate our new online privacy state.
Finally, reviewing our Facebook, Twitter or similar accounts to remove old content is a good practice to delete internet presence. Sometimes this information may be used against us; it may even serve to find more personal information. A threat actor committed to attacking us will surely use any old tweet or Facebook status to find greater references and put us at risk.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











