A US Government defense agency that provides technology services to multiple senior officials, including the president, has revealed that their networks could have been compromised. Through a series of letters sent to potentially affected people, the Defense Information Systems Agency (DISA) revealed a data breach involving one of its critical systems, digital forensics specialists say.
According to the information leaked so far, the data breach took place between May and July 2019, compromising sensitive data such as names, email addresses, Social Security numbers, among other details of members of the organization and collaborators in other areas of US Defense. It is so far unknown whether the information was stored on a classified system.
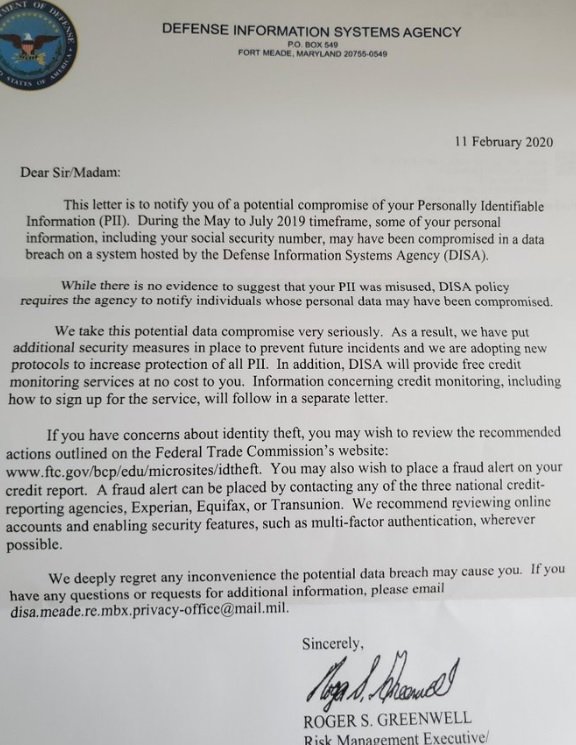
Although there was initially no official confirmation, Charles Prichard, DISA’s spokesperson, acknowledged the incident through a statement: “We have begun to notify people whose confidential information could have been compromised during this data breach in one of the systems hosted by DISA,” the spokesman says.
Although DISA mentions that no evidence of malicious use of compromised information has been found, digital forensics specialists consider it relevant that a protocol for protecting the information exposed be implemented.
Regarding the potential perpetrators of the incident, it is not ruled out that it is attributed to any group of threat actors sponsored by any US adversarial country, especially after the US government’s resolution on the security incident at Equifax. A few days ago, the Department of Justice (DOJ) charged four members of China military for their alleged involvement in the hacking against the financial firm, which ended in the exposure of more than 140 million confidential financial reports.
According to digital forensics specialists from the International Institute of Cyber Security (IICS), the DOJ has also attributed to Chinese hackers other relevant incidents related to data breaches, such as that at the Marriott hotel chain, although no Chinese government or army official has been formally charged regarding these attacks.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











