A recent report by participants of a cyber security course mentions the presence of a flaw that makes it possible to extract sensitive information from AMD processors, manipulating the L1D cache predictor with two variants of different attack. Researchers claim that the vulnerability exists in all processor models that the company launched between 2011 and 2019, implying that Zen architecture is also compromised.
According to the researchers, the vulnerability in AMD is related to a side-channel approach, as is the case with the most dangerous variants of processor attacks. By deploying attacks based in Spectre, the experts, in the role of threat actors, were able to access information on the supposedly protected processor.
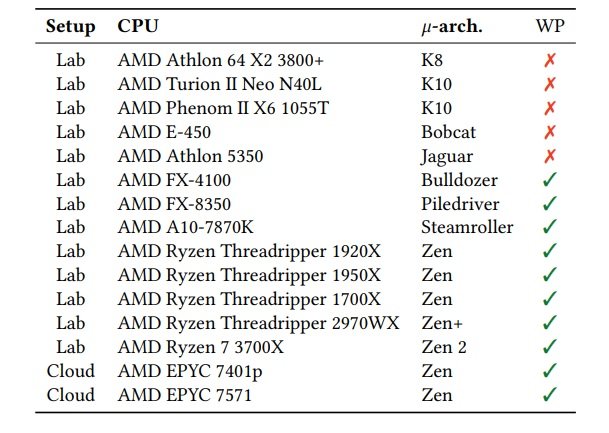
“Reverse engineering the L1D predictor on architectures launched between 2011 and 2019, we discovered these two new attack techniques,” the cyber security course members mention. The first of these techniques, dubbed ‘Collide+Probe’, allows a threat actor to monitor any access to the target user’s memory without knowing locations in the system.
On the other hand, the second attack, called ‘Load+Reload’, allows the predictor to be exploited to obtain traces of access to the victim’s memory. This second attack is even more stealthy than the previous one, the report mentions.
Cyber security course participants were able to exploit the flaw using JavaScript code run in Chrome and Firefox. In their research specialists mention that the vulnerability could even be exploited to access cloud deployments. Although the research outlines several possible ways to mitigate failure (based on a combination of hardware and software improvements), the impact these solutions would have on the performance of the affected devices is not yet contemplated.
After receiving the report, AMD issued a message stating that no mitigation is necessary, as already released fixes to prevent the exploitation of other side channel flaws are sufficient. However, the researchers disagreed with the company’s position, stating that the active exploitation of this flaw is a possibility that must be seriously considered.
According to the International Institute of Cyber Security (IICS) due to the complexity in the design and capabilities of modern processors, it is a fact that all these devices contain security vulnerabilities, all that’s left to do is keep working in the finding of those security flaws before threat actors do so.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











