Nearly two years ago, researchers from a pentesting course company revealed that the Marriott hotel chain had been the victim of one of the largest data breach incidents recorded so far, compromising personal information of around 500 million customers of the Starwood subsidiary.
When everyone thought Marriott would have already implemented the necessary measures to prevent these incidents from happening again, a report has been leaked stating that the company has suffered a new data breach that compromised the information of nearly 2.5 millions of users.
According to the experts of the pentesting course company, this incident occurred in mid-January because a threat actor managed to extract the login credentials of one of the employees of the hotel chain, entering multiple systems of guest storage. Among the data presented are details such as:
- Full names
- Addresses
- Email addresses
- Phone numbers
- Dates of birth
- Booking data
Anomalous activity went unnoticed by Marriott’s IT security teams for weeks; Finally, during the last days of February, the company detected the intrusion, disabled compromised access and began an investigation into the incident to notify all potentially affected users.
Although no one denies that the hotel chain should be held accounted for for the security of its users’ information, it should be noted that these recent incidents initiated as attacks against third-party companies providing some administrative services to Marriott, so they didn’t compromise their internal networks. As experts from a pentesting course company point out, the 2018 incident was due to the attack on Starwood databases, which would be acquired by Marriott shortly thereafter.
The International Institute of Cyber Security (IICS) says the most recent incident affected about 5.2 million customers in the chain, all members of its loyalty program; the company is in the process of notifying potentially affected customers.
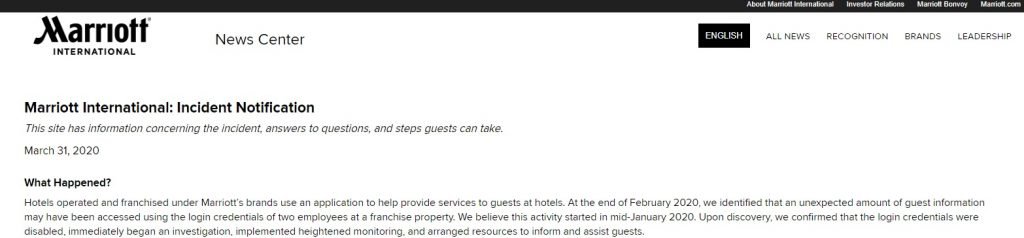
Users concerned about the security status of their personal information may also check the platform Marriott has put online to resolve questions related to this incident, although this may not be the best of the ideas given by the recent history of data protection of the company.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











