IT security services specialists mention that OpenSSL Project developers have released an OpenSSL security update to fix a severe vulnerability; tracked as CVE-2020-1967, exploiting this vulnerability would allow malicious activities such as denial of service (DDoS) to be deployed. This is the first vulnerability corrected by OpenSSL in 2020.
The developer report mentions that this vulnerability is a segmentation error in the SSL_check_chain function: “Server or client applications that call the function SSL_check_chain during or after a TLS 1.3 handshake may crash due to NULL pointer dereference as a result of incorrect handling of the TLS extension” , mentions OpenSSL Project.
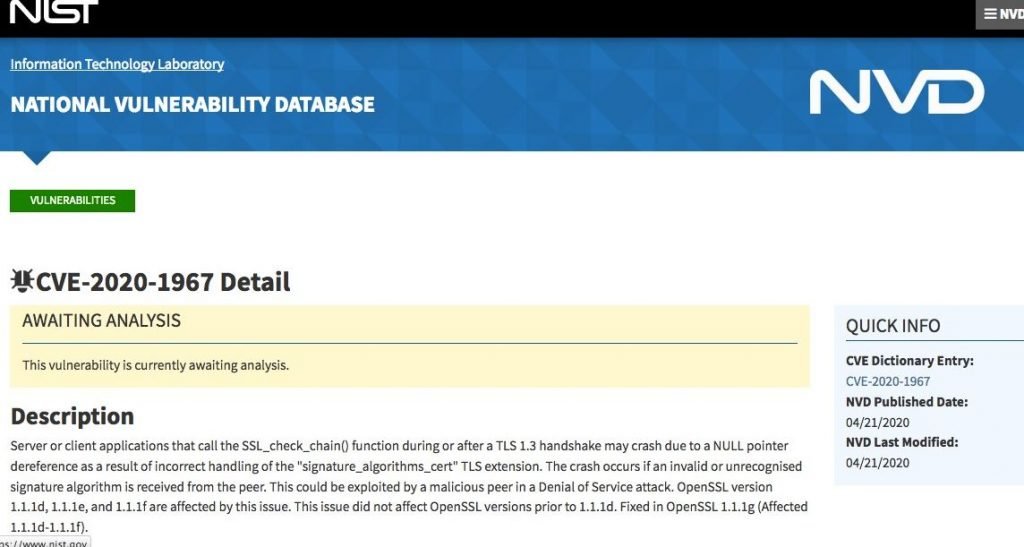
According to the IT security services specialists this system collapse occurs if an invalid or unrecognized signature algorithm is received from the peer. This could be exploited by a threat actor in a denial of service (DDoS) attack. The vulnerability is present in OpenSSL versions 1.1.1d, 1.1.1e, and 1.1.1f. This vulnerability was fixed with the release of version 1.1.1g.
It should be noted that previous versions (1.0.2 and 1.1.0) do not appear to be affected by the vulnerability, so administrators of these versions do not need to install updates.
The IT security services experts discovered the vulnerability on April 7. For the finding, the researchers used the new static analysis pass implemented in the GNU Compiler Collection (GCC) static code analyzer. Additional analysis results will be revealed as soon as possible.
The OpenSSL security alert concludes by mentioning: “This inconvenience is not present in version 1.0.2, however, these versions are not supported and have stopped receiving support; an extension in support is available to Premium customers.” In addition, the issue does not affect OpenSSL 1.1.0; however, these versions are not supported and no longer receive updates. Users of these versions should upgrade to OpenSSL 1.1.1.
For further reports on vulnerabilities, exploits, malware variants and computer security risks you can access the official website of the International Institute of Cyber Security (IICS), as well as the official platforms of technology companies.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











