A couple of weeks ago, information security awareness specialists from Wordfence detected a vulnerability in Real-Time Find and Replace, a popular WordPress plugin active on more than 100,000 sites operated by this content management system (CMS).
If exploited, this flaw could allow threat actors to inject malicious JavaScript code into any sector of the affected site; To do this, all attackers require is to trick the administrator into downloading a document, clicking on a link or opening an email.
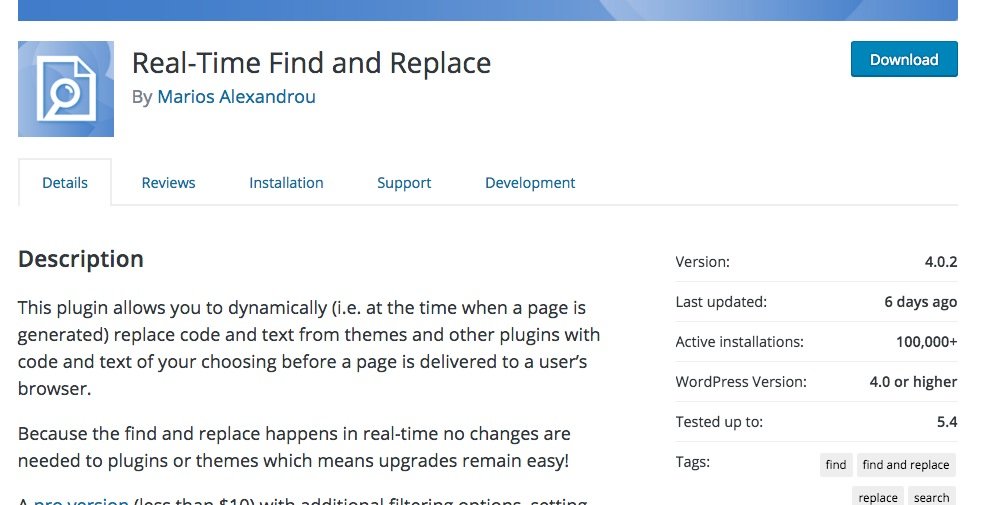
The developers were notified about the finding on April 22; hours later an update patch had already been released. This was considered a serious cybersecurity threat, so information security awareness experts recommend users of the affected plugin update to the latest version (v4.0.2). Below are some technical details about the vulnerability.
Real-Time Find and Replace provides a feature to dynamically replace any HTML content on WordPress sites, placing new content without permanently changing the original content. New data is uploaded immediately, before it is delivered to the WordPress site visitor’s browser.
To provide this functionality, the add-in registers a submenu page linked to the function far_options_page with an ability requirement to activate plugins.
The far_options_page function contains the core of the add-in’s functionality for adding new search and replacement rules. Unfortunately, that feature was unable to use nonce verification, so the source integrity of a request is not verified during the rule update, triggering a cross-site request forgery (XSRF) flaw, information security awareness experts mentioned.
If threat actors manage to trick the target site administrator into taking any action, they could replace the content or HTML, showing visitors a vulnerable site riddled with malicious content. The content of the attackers will be displayed when the user enters the compromised web page.
An attacker could use this vulnerability to replace an HTML tag as <head> with malicious Javascript. This would cause the malicious code to run on almost every page of the affected site, as almost all pages start with an HTML tag <head> for the page header, which creates a significant impact if successfully exploited.
For further reports on vulnerabilities, exploits, malware variants and computer security risks you can access the website of the International Institute of Cyber Security (IICS), as well as the official platforms of technology companies.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











