Introduction
HiveJack is an internal penetration testing tool and it can be used on compromised windows machine or where you have physical access to the machine on Internal Network. This tool can be used to collect the Windows credentials from the compromised machine.
This tool dumps SYSTEM, SECURITY and, SAM hives from the machine, which later on can be used to retrieve the list of windows username and even the password.
Environment
- OS: Microsoft Windows [Version 10.0.18363.720]
- PROCESSOR_ARCHITECTURE: AMD64
Execution Steps
- The HiveJack tool is easy to use. There is no installation needed for this tool.
- Just simply download the HiveJack.ex file and execute the tool.
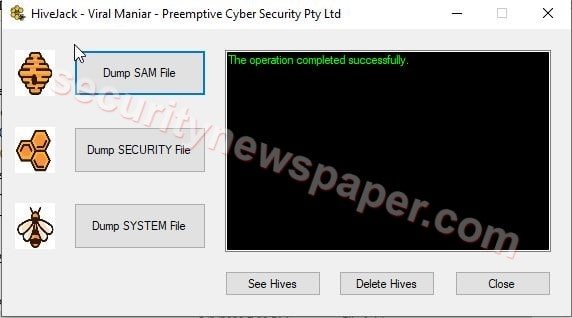
- We will see the tool in this way.

- In the above picture, we have different file dumps options.
- In the HiveJack tool, there is no stress to remember the commands.
- Here, we clicked on Dump SAM File to dump SAM file in C:\temp folder.
- Now click on Dump SECURITY File to dump SECURITY file in C:\temp folder.
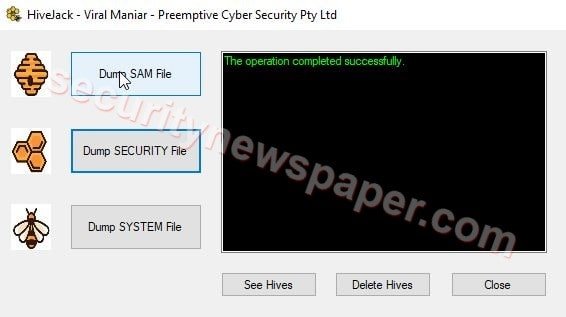
- Then click on Dump SYSTEM File to dump SYSTEM file in C:\temp folder.

- In the above steps we have successfully collected all three different files from the Windows machine and now let’s check the files in C:\temp folder.
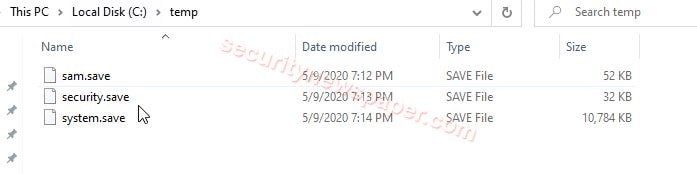
- All three files are stored in C:\temp folder.
- Now, let’s copy the temp folder to our Kali Machine to cracking the password.
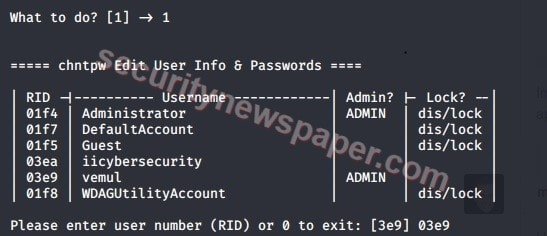
- After copying with the file in Kali, go to the file path and type this command chntpw -I sam.save to retrieve the usernames in Windows machine.
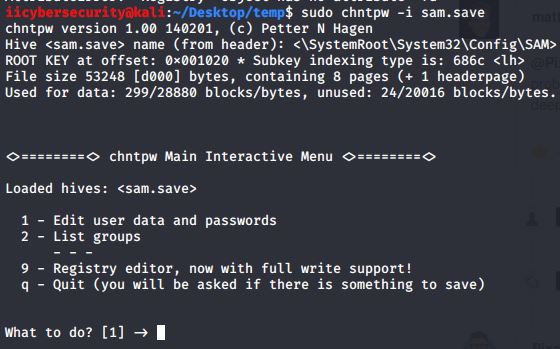
- Here, chntpw Main Interactive Menu , you can select option 1, to edit user data and password.
- So we can see that the system has iicybersecurity, vemul users other than Administrator user.
- We can also used retrieve the passwords in Windows using the steps mentioned here, Crack the Windows password with John the Ripper.
Conclusion
So we saw on the easy way to retrieve the Windows credentials in less time.

Cyber Security Specialist with 18+ years of industry experience . Worked on the projects with AT&T, Citrix, Google, Conexant, IPolicy Networks (Tech Mahindra) and HFCL. Constantly keeping world update on the happening in Cyber Security Area.











