According to network perimeter security specialists, Apache Spark developers have just officially released a remote code execution risk alert that affects their software. The vulnerability was tracked as CVE-2020-9480 and received a high score on the Common Vulnerability Scoring System (CVSS).
It should be remembered that Apache Spark is an open source framework for distributed general purpose cluster computing. Spark provides an interface for programming entire groups with implicit data parallelism and flaw tolerance.
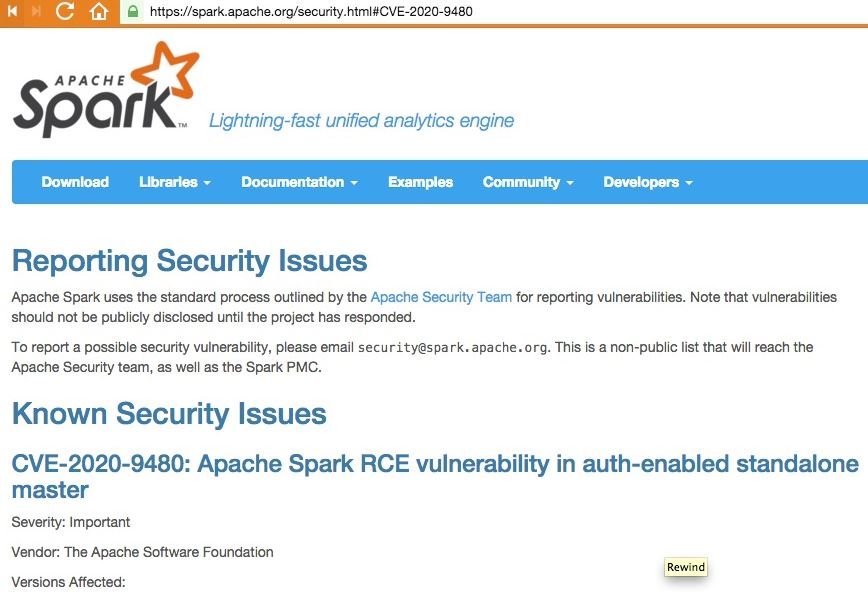
Network perimeter security specialists point out that in Apache Spark 2.4.5 and earlier, the stand-alone resource manager principal server can be configured to require authentication through a shared key (spark.authenticate).
Because of some spark authentication mechanism flaws, shared key authentication fails. Threat actors might abuse this vulnerability for command execution on the host without administrator authorization, which would result in remote code execution.
“In Apache Spark 2.4.5 and earlier, a stand-alone resource manager master can be configured to require authentication (spark.authenticate) through a shared secret. However, when enabled, an RPC specially designed for the master can succeed when starting an application’s resources in the Spark cluster, even without the shared key. This can be exploited to take advantage of shell commands on the host machine,” the Apache alert mentions.
The vulnerability resides in all versions of Apache Stark after 4.2.5, mentioned by network perimeter security experts.
Fortunately, developers have already released fixes for these bugs, so Apache Stark users should only upgrade to version 2.4.6, or to 3.0.0. For further reports on vulnerabilities, exploits, malware variants and computer security risks, it is recommended to enter the website of the International Institute of Cyber Security (IICS), as well as the official platforms of technology companies.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











