The most recent months have been marked by the multiple racial protests in various parts of the world, mainly in the US, which has led (among many other things) to rethinking the use of some words, which has not gone unnoticed by the cybersecurity and computer science community.
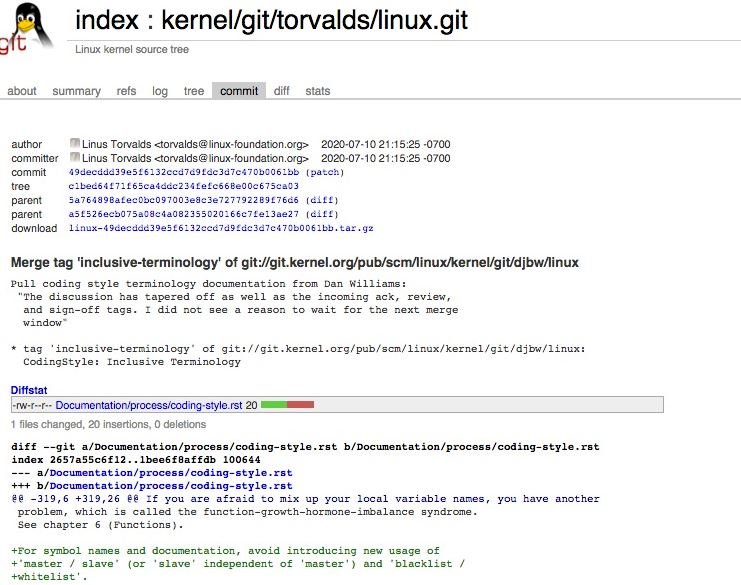
According to experts in a cyber security course, Linus Torvalds has just approved the use of new and more inclusive terminology in Linux kernel code and documentation. Consequently, Linux developers will need to use new terms to replace the use of <<master/slave>>, <<blacklist/whitelist>>, among others.
Among the proposed alternatives to replace the terms master/slave are:
- Primary – Secondary
- Main – Replica
- Initiator – Target
- Applicant – Responder
- Driver – Device
- Host – Worker or proxy
- Leader – Follower
- Director – Performer
On the other hand, the proposed alternatives to replace blacklist/whitelist include:
- denylist – allowlist
- blocklist – passlist
Linux managers did not recommend using any specific term, so developers, cyber security course experts, and other users will be able to choose the one they think is best. The new terminology may be used for the new Linux kernel source code and any articles, reviews, technical descriptions or any document associated with the operating system.
The terms used above, and which are now considered inappropriate, will be used for the maintenance of code and related documentation, in addition to their use in updates to specific code where only such terms are supported.
These changes were proposed by Dan Williams, head of the Linux kernel, at the beginning of July. Torvalds, creator of the operating system, approved the proposal a few days ago, sending a pull request for the Linux 5.8 repository.
This is how Linux developers have joined an emerging movement in the computer community that seeks to eliminate the use of terms that might be considered racist, opting for the implementation of a more neutral terminology. To this initiative have been added firms such as Twitter, GitHub, Microsoft, LinkedIn, Ansible, Splunk, Android, Go, MySQL, among others, as mentioned by the specialists of the cyber security course.
For further reports on vulnerabilities, exploits, malware variants and computer security risks, it is recommended to enter the website of the International Institute of Cyber Security (IICS), as well as the official platforms of technology companies.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











