Hacking campaigns between the governments of Israel and Iran continue to increase, as mentioned by information security awareness specialists. According to recent reports, a group of Iranian hackers would have deployed a series of cyberattacks against Israel’s rail infrastructure, an attack that has remained active since mid-July.
The alleged hacker group, self-appointed Cyber Avengers, released a statement on multiple Telegram channels, ensuring that they managed to attack the industrial servers of the Israeli railways, compromising operations at more than 28 train and subway stations. This group is presumed to be linked to the Iran Revolutionary Guard (IRGC).
According to information security awareness specialists, this ambitious hacking campaign would have begun in the early morning of July 14, lasting for at least 10 days. The intrusion was detected by Israeli authorities on July 24, although hackers warned that this is only the beginning and the worst is yet to come.
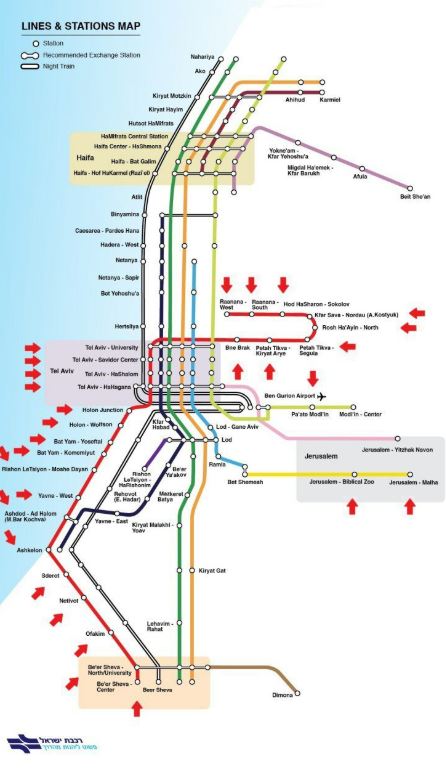
A map published by the attackers mark to the 28 compromised stations, including Jerusalem, Tel Aviv University and Ben Gurion. A few days after the operation ended, multiple stations remained out of service due to severe infrastructure damage caused by the attack.
Regarding the reasons for attacking Israeli rail infrastructure, the hackers only mentioned that they were seeking “to demonstrate their planning skills”, adding that they could have even caused fatal accidents if they wanted to. Although this hacking group was credited with the recent massive power failures in Israel, no firm or information security awareness experts have confirmed the origin of these attacks.
Governments allegedly involved in these incidents have not spoken out about the signs, although it is a fact that both nations are going through a political tension. Cyberwarfare campaigns would have begun last April, when multiple wastewater treatment plants in Israel were compromised using sophisticated cyberattack techniques. Another major incident occurred in Iran, when some fires occurred at Iranian nuclear facilities. Authorities did not provide further reports on the causes of these fires, although some speculate on a possible hacking campaign.
For further reports on vulnerabilities, exploits, malware variants and computer security risks, it is recommended to enter the website of the International Institute of Cyber Security (IICS), as well as the official platforms of technology companies.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











