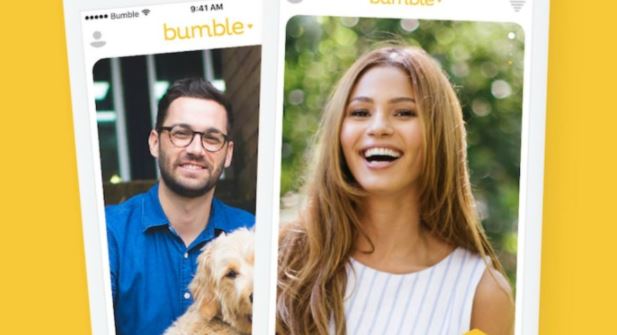
Security specialist Sanjana Sarda performed a thorough analysis of the code of the popular Bumble dating app, discovering multiple API vulnerabilities that could expose the information of the platform’s nearly 100,000 users.
The researcher claims it is really easy to detect these problems, although the response she received from developers demonstrates the little seriousness with which the company addresses these issues even though they even have a rewards program powered by HackerOne.
“While API issues are not as exploited as other failures, these attacks can cause significant damage,” says Sarda, who reverse engineered the Bumble API and found multiple endpoints that processed actions without being verified by the server. Because of this, the limitations of Premium services on the platform could be evaded by any user with a standard subscription using the Bumble web app instead of the mobile app.
Sarda mentions that she was also able to use the Bumble Developer Console to access information from Beeline, one of the Premium features in Bumble that allows you to view the information of all users interested in a profile. However, the most telling thing Sarda found is that the API allows access to the “server_get_user” endpoint to list Bumble users around the world and even retrieve Facebook data associated with dating app profiles, not to mention that it was also possible to access information such as political affiliation, astrological sign, and educational level, among others.
Finally, the researcher mentions that vulnerabilities could also allow threat actors to analyze whether a target user has the Bumble app installed on their device and even calculate their location with a high degree of accuracy.
Although Sarda and her team reported their findings to Bumble, although after more than 200 days without a response they decided to disclose their findings: “After publishing the report we received an email from HackerOne, although the deadlines set by the cybersecurity community were already expired,” she adds.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











