A database of information from virtually all registered voters in the United States has been leaked. These logs are on sale in various hacking forums, exposing affected users to multiple scam attempts and dangerous cyberattacks.
The database contains voter information in states such as Colorado, Connecticut, Michigan, North Carolina, Oklahoma, Rhode Island, Delaware, Florida, and New York, as mentioned by the specialists from the International Institute of Cyber Security (IICS).
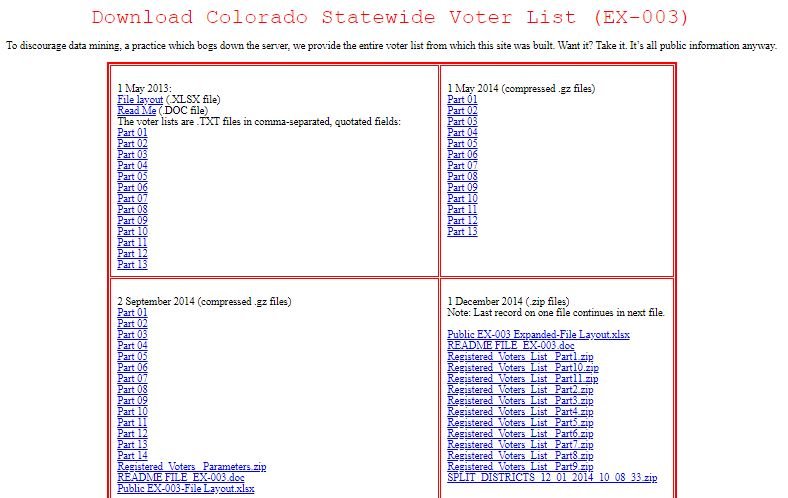
For Colorado:
http://coloradovoters.info/download.html
For Conneticut
http://connvoters.com/download.html
For Michigan
http://michiganvoters.info/download.html
For North Carolina
https://dl.ncsbe.gov/index.html?prefix=data/
For Oklahoma
http://oklavoters.com/download.html
For Rhode Island
http://rivoters.com/
For Delaware
http://delawarevoters.info/downloads.html
For Florida
http://flvoters.com/downloads.html
For New York
http://form.jotform.us/form/50913672751154
According to the reports, the records exposed contain very detailed information about users, including their political affiliation. Sellers of this information claim that they have nearly 190 million records or, in other words, a significant portion of total U.S. voters.
In their report, IICS experts mention that this information could be used by threat actors to deploy complex social engineering campaigns or even with the intention of intervening in U.S. electoral processes, especially in states where there is the greatest dispute between the two political parties.
Experts also mention that some of the data comes from public sources, although most of the records were obtained in data breach incidents. Other databases with similar records from countries such as England, Canada, Ireland and South Africa were also detected.
However, the main objective of cybercriminals appears to be the monetization of compromised information, which includes personal data such as full names, dates of birth, gender, in addition to the political affiliation of affected citizens. Although it has been a couple of weeks since the U.S. presidential election, investigators do not rule out these intervention campaigns remaining active, so it is best to keep your information protected to prevent it from reaching the hands of threat actors.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











