SQLite security teams announced the release of a security patch to mitigate a vulnerability that would have allowed arbitrary code execution or deployment of denial of service (DoS) attacks. The developer security alert mentions that this failure primarily affects systems that use a C-language library that implements a SQL database engine due to system availability.
Despite the apparent severity, the report mentions that this is a failure of average severity because its exploitation depends on threat actors having access to queries in the databases attacked. On the other hand, Richard Hipp, the chief engineer responsible for SQLite considers the flaw not a serious threat, although he did not ignore the report.
In the event of an SQL injection flaw on the target system, this condition could lead to SQLite reading a previously released data write with the possibility of causing a crash: “SQLite will most likely return an unusual response. This issue allows threat actors to scale vulnerabilities and deploy DoS attacks,” Hipp adds.
The cybersecurity community mentions that because developers consider this flaw to have a moderate impact, other applications may also be affected. Considering that SQLite is an open source development, it is likely to be used more than any other database engine millions of websites could be exposed. On the other hand, the database management system is integrated into more than 3 billion smartphones, as well as all macOS and Windows 10 devices, Firefox, Chrome and Safari browsers, as well as services such as Skype and Dropbox.
Inti De Ceukelaire, specialist at security firm Intigriti, believes that claiming that this is a moderate severity vulnerability could represent a false sense of security for some system administrators: “The worrying thing about such flaws is that providers choose not to update as the actual impact is minimal; While this flaw can only be exploited under very specific conditions, suppliers should take into account the potential risks of leaving flaws unpatched.”
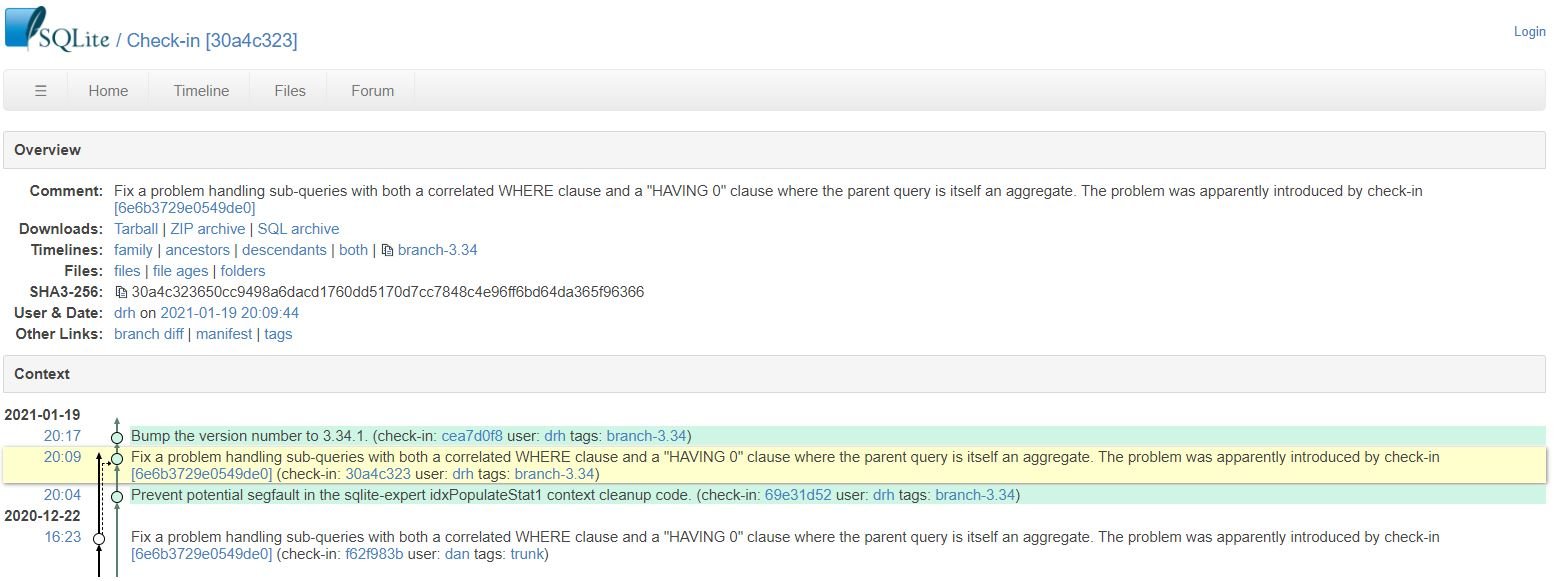
SQLite developers resolved this flaw by adding “ExprAlwaysFalse (pExpr)-0 to the if declaration before the business logic in havingToWhereExprCb() in the src/select.c file, so vulnerable deployment administrators are advised to update as soon as possible.
To learn more about computer security risks, malware, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) website.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











