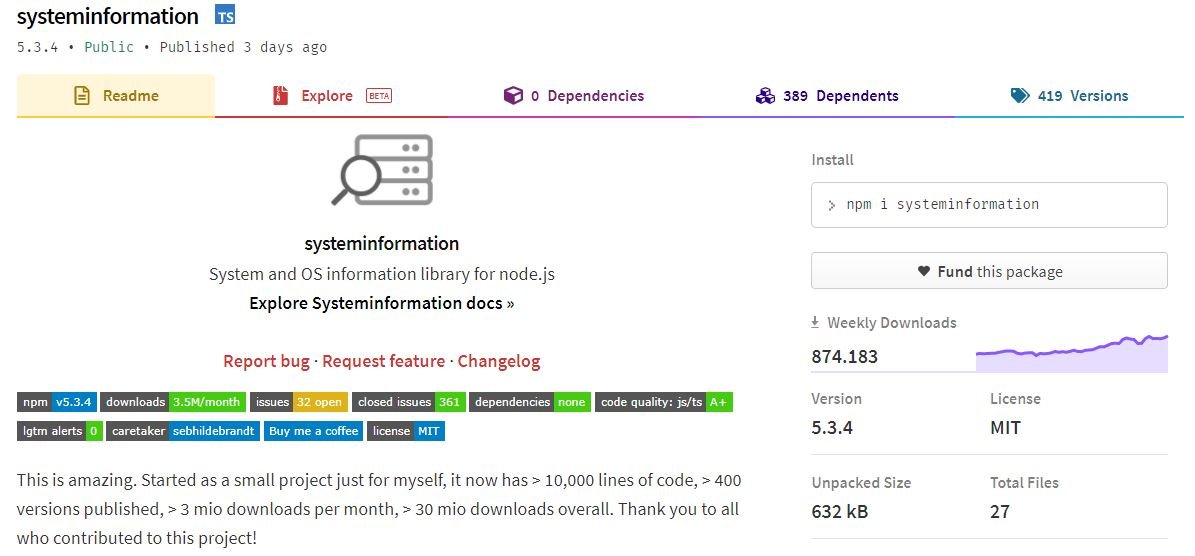
The development team behind systeminformation announced the patching of a severe security flaw that exposed vulnerable applications to arbitrary command injection attacks in the popular Node.js package. As you may remember, systeminformation provides dozens of features to retrieve hardware and software information from servers hosting Node.js applications and has more than 850,000 downloads per week from its official GitHub repository.
This attack variant allows any threat actor to manipulate an application by sending system-level commands to the host server. If a function inserts user input strings into system commands without proper reviewing them, a malicious hacker can take advantage of this failure for the function to execute arbitrary system-level code.
Sebastian Hildbrandt, the main maintainer of the software, mentions that systeminformation is not intended for use in conjunction with user input: “The situation with systeminformation is that it is a package intended for use in the backend; the intention was for developers to use this software as carefully as possible.”
The software maintainer also mentions that in some cases, developers open some of the library functions to their end users, allowing the passage of parameters that will eventually be sent to the systeminformation package: “This package includes a set of disinfection functions that provide basic parameter verification. Maintainers are oblivious to the context in which these packets are handled,” Hildebrandt adds.
After analyzing the situation it was reported that four systeminformation features are vulnerable to this arbitrary command injection attack, a condition that could be related to a special case of incorrect parameter verification and array debugging. Hildebrandt adds that if the input was not debugged and users could move from a JavaScript array as a parameter to the given functions, this could become an arbitrary code execution scenario, thus leading to denial of service (DoS) conditions on the vulnerable system.
The flaw has already been corrected and received a medium-severity score based on the scale used by GitHub. The library maintainer team recommends that developers update their version of this package, in addition to publishing the list of vulnerable features, which will allow better debugging of potentially risky entries to completely avoid the occurrence of the flaws described in the report. To learn more about information security risks, malware, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) website.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











