A former employee of SpaceX, the aerospace company property of the renowned millionaire Elon Musk, acknowledged that he was involved in the operation of a security fraud that led to the publication of private information on the dark web.
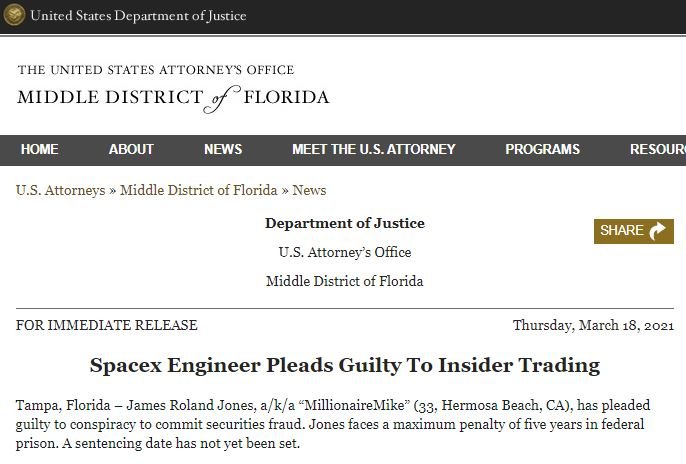
According to documents filed by the US Department of Justice (DOJ), software engineer James Rolando Jones, a California resident, pleaded guilty to trafficking sensitive SpaceX information on a dark web platform, acknowledged his involvement in a conspiracy to commit fraud and in the purchase and sale of business secrets.
The investigation involved the involvement of an undercover agent from the Federal Bureau of Investigation (FBI), with whom the defendant shared multiple details of his fraudulent activities.
Between 2016 and 2017, the defendant purchased names, dates of birth and social security numbers on the dark web in order to create fake accounts and transact using sensitive information. In addition to the charges filed by the DOJ, Jones faces separate accusations from the Securities and Exchange Commission (SEC) relating to access to confidential information and the sale of data on the dark web.
The SEC claims that Jones violated the provisions of multiple anti-fraud laws, extracting private information to exchange it on illegal hacking platforms.
Jones is awaiting his sentence, which could reach up to 5 years in prison; It should be remembered that the highest sentence imposed by U.S. law is 12 years in prison, which attorney Matthew Kluger currently serves in a federal prison.
The defendant reached an agreement with the SEC to turn himself in and agree on a reduction in his conviction in exchange for cooperating with the authorities in the investigation of this case and similar ones. On the other hand, SEC Regional Director David Peavler believes this is a great example of the agency’s work: “In this case show that the SEC can prosecute and prosecute securities law violators wherever they operate, even on digital platforms. We have the best personnel and technology to pierce the cloak of anonymity with which these criminals try to cover their tracks.”
What do you think of these cybercriminal practices? Do you think the authorities are doing enough to mitigate the activities of threat actors? To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











