Cybersecurity specialists reported the finding and patching of two security flaws in vRealize Operations, a popular VMware technology company solution. According to the report, successful exploitation of these flaws would have posed severe risks for vulnerable system administrators.
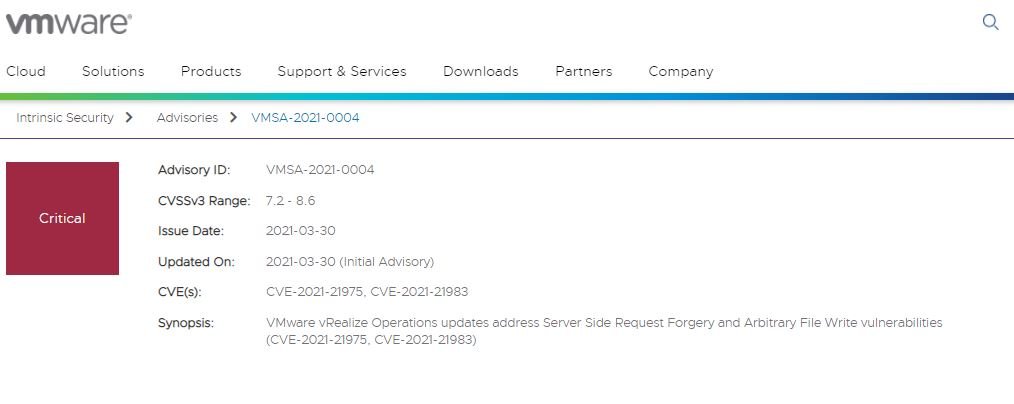
These flaws, tracked as CVE-2021-21975 and CVE-2021-21983, reside in the vRealize Operations Manager API, and were described as server side request forgery (SSRF) and binary writing errors.
In its report, VMware notes that the request forgery vulnerability would allow threat actors with network access to the API to obtain administrator credentials, while the second flaw would allow an authenticated malicious hacker to write files to arbitrary locations on the Photon operating system.
The report was presented by Egor Dimitrenko, a specialist at Positive Technologies, who mentions that flaws can be exploited in a chained way to lead to an arbitrary code execution scenario on the affected servers. Dimitrenko added that attacks in the wild would have allowed hackers to get an entry point into the affected system, leading to all sorts of risk scenarios.
VMware security teams released security patches for all affected versions, as well as fixing some flaws in vRealize Suite Lifecycle Manager. The company notes that these vulnerabilities received high scores in the Common Vulnerability Scoring System (CVSS). Affected deployment administrators should update as soon as possible to fully mitigate the risks associated with exploiting these flaws.
Although the flaws have already been fixed, experts do not rule out the possibility that some hacking group could have successfully exploited in real-world scenarios, as multiple scans were detected in early 2021 days before security patches were released. However, the proof of concept (PoC) code was quickly made available to vulnerable administrators, so it was possible to mitigate the risk of exploitation to some extent.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) website.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











