The Azure Defender for IoT research group reported the finding of at least 25 security flaws impacting all kinds of intelligent devices and industrial application Internet of Things (IoT) equipment. This set of vulnerabilities, identified as “BadAlloc”, was identified by experts from Microsoft and the Cybersecurity and Infrastructure Security Agency (CISA).
According to the report, failures exist in standard memory allocation functions spanning real-time operating systems (ROTS), software development kits (SDKs), and C-standard library implementations. As the name implies, memory allocation features allow developers to control how a device’s firmware and applications work with the device’s built-in physical memory.
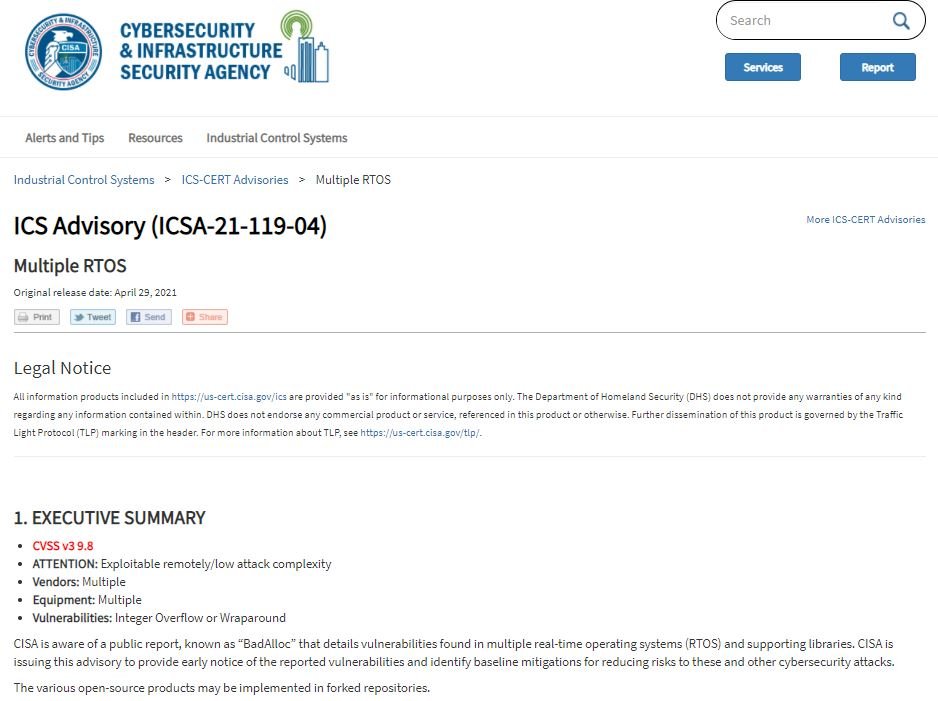
Researchers mention that BadAlloc flaws occur because memory allocation implementations written for IoT devices and integrated software have not incorporated proper input validation: “Without this protection mechanism, an attacker could exploit the memory allocation function to perform a stack overflow that could lead to the execution of malicious code in a compromised deployment.” In addition, attacks can be deployed remotely if vulnerable devices are exposed on the Internet.
In the report, the company confirmed that problems were encountered with entry validation in the following products:
- Amazon FreeRTOS, v10.4.1
- Apache Nuttx OS, v9.1.0
- ARM CMSIS-RTOS2, versions prior to 2.1.3
- ARM Mbed OS, v6.3.0
- ARM mbed-uallaoc, v1.3.0
- Cesanta Mongoose OS Software, v2.17.0
- eCosCentric eCosPro RTOS, v2.0.1 to v4.5.3
- Google Cloud IoT Device SDK, v1.0.2
- Linux Zephyr RTOS, versions prior to 2.4.0
- Media Tek LinkIt SDK, versions prior to 4.6.1
- Micrium OS, v5.10.1 and earlier
- Micrium uCOS II / uCOS III v1.39.0 and earlier
- NXP MCUXpresso SDK, v2.8.2 and earlier
- NXP MQX, v5.1 and earlier
- Redhat newlib, prior to v4.0.0
- RIOT OS, v2020.01.1
- Samsung Tizen RT RTOS, prior to v3.0.GBB
- TencentOS-tiny, v3.1.0
- Texas Instruments CC32XX, prior to v4.40.00.07
- Texas Instruments SimpleLink MSP432E4XX
- Texas Instruments SimpleLink-CC13XX, prior to v4.40.00
- Texas Instruments SimpleLink-CC26XX, prior to v4.40.00
- Texas Instruments SimpleLink-CC32XX, prior to v4.10.03
- Uclibc-NG, prior to v1.0.36
- Windriver VxWorks, prior to v7.0
On the other hand, CISA notes that only 15 of the 25 affected deployments released security updates to fix these failures, although the remaining ones are expected to be fixed over the next few months.
While updates are available, CISA and Microsoft recommend that affected organizations reduce exposure to vulnerable devices, as well as implement monitoring mechanisms for potential anomalies and segment internal networks to contain a potential exploitation case.
So far, no cases of active exploitation of any of these failures have been detected, although administrators should not be neglected for a second. To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











