Cybersecurity specialists reported the finding of two vulnerabilities in Joomla, one of the most popular content management systems (CMS) nowadays, with more than 1.5 million active users. Experts describe these flaws as a password reset error and a cross-site scripting (XSS) flaw that could be chained together to lead to the total compromise of a target system.
The report was published by researchers at the security firm Fortbridge, and revealed in compliance to the cybersecurity community guidelines. Joomla developers received the reports in March 2021.
After receiving the report, Joomla began work on releasing a security patch to address the XSS flaw; CMS version 3.9.2 contains such an update. Moreover, the password reset failure will be corrected with a “trusted_hosts” setting.
Adrian Tiron, a member of Fortbridge’s research team, says the flaws are highly severe and their chained exploitation would allow threat actors to deploy severe attacks: “If attackers fully access Joomla’s website, they could load a php shell to execute commands on the server,” Tiron notes.
As mentioned above, the first flaw would allow threat actors to reset an administrator password: “Malicious hackers activate the password reset process, manipulate the reset link, and redirect it to their own server, allowing them to capture the victim’s token and set a new password”, Tiron states.
The abuse of the XSS vulnerability depends on the success of the first attack: “Once attackers reset the password and gain administrator privileges, it is possible to use an XSS attack to compromise the “super admin” user.
By increasing their privileges to “super admin”, malicious hackers can gain full access to the system and the ability to deploy a remote code execution (RCE) attack against a vulnerable Joomla implementation. The expert believes that this problem exists because the developers of the CMS used a block list to prevent the use of malicious extensions, although they forgot to block .html.
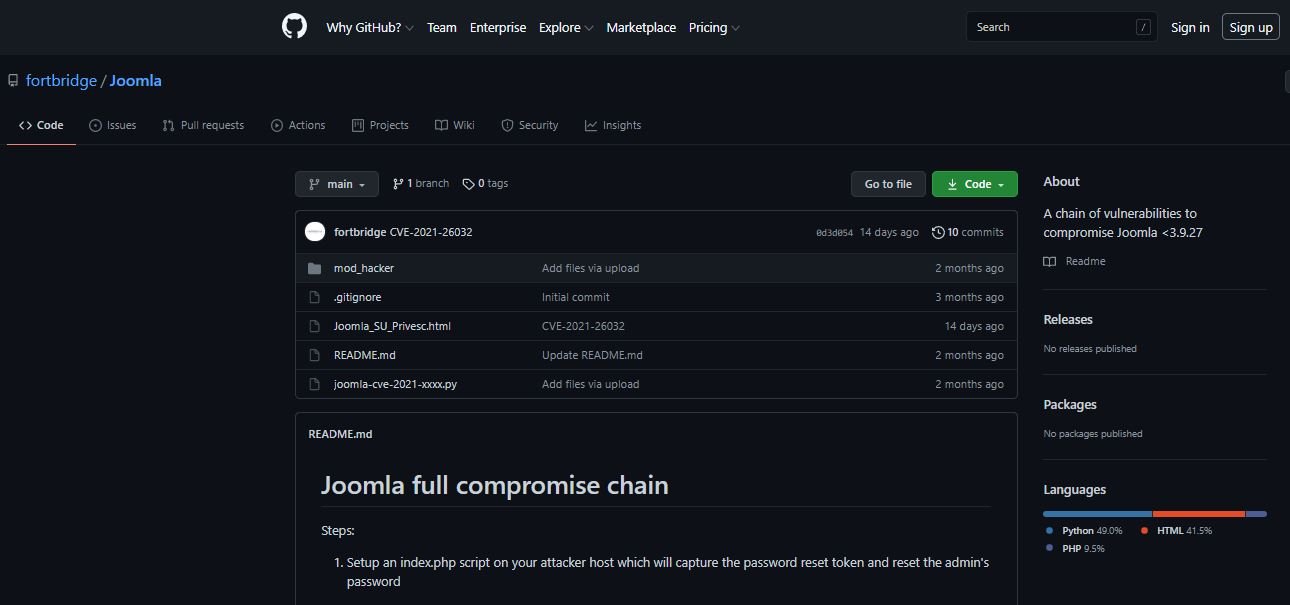
Fortbridge published a detailed description of the vulnerabilities on its official platforms, in addition to publishing a proof of concept (PoC) code on GitHub. Joomla received some requests for information from members of the cybersecurity community, although the company has not commented on the matter.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











