Cybersecurity experts report that a proof of concept (PoC) exploit and technical details related to an unpatched vulnerability in Windows systems have been leaked online by accident.
The vulnerability in question, identified as PrintNightmare, affects the Windows Print Spooler and its exploitation would allow threat actors to take control of a Windows domain server and deploy malware in enterprise environments. Reports from multiple researchers claim to have successfully tested the leaked PoC exploit on fully updated Windows Server 2019 systems.
The leak of the details of this vulnerability occurred by accident and due to a confusion with CVE-2021-1675, another flaw that resides in Print Spooler and was corrected in early June. At the time of its disclosure, Microsoft determined that this was a highly severe privilege escalation flaw, though the company later changed its rating to critical without providing further information.
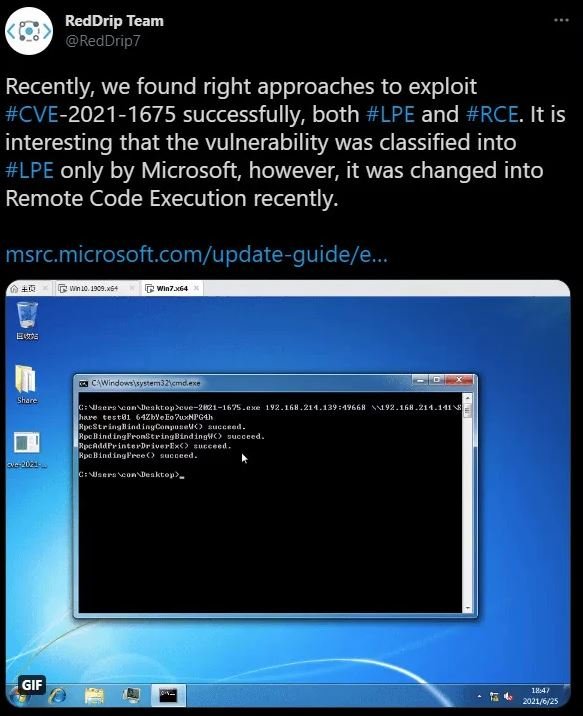
Although several companies were investigating this incident, Chinese security company QiAnXin reported a method to exploit the vulnerability in order to deploy the local privilege escalation condition, in addition to a remote code execution condition.
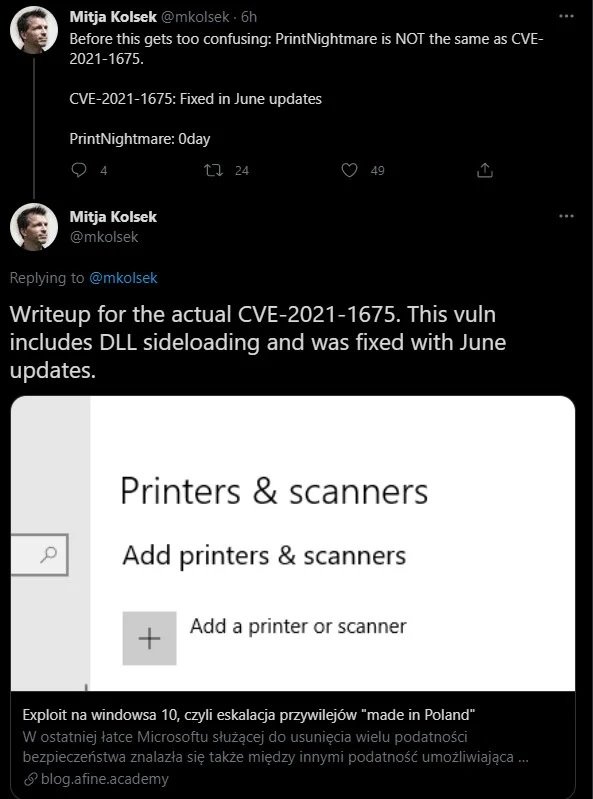
Although at first it was thought that everything was part of the same vulnerability, soon after it was discovered that PrintNightmare is not the same flaw as CVE-2021-1675, but a zero-day vulnerability in Windows Print Spooler that to date has not been fixed by the manufacturer.
Mitja Kolsek, CEO of Acros Security took time out of the confusion, noting that the technical details released for CVE-2021-1675 are different from what was published at the beginning.
Beyond the confusion over the reports, PrintNightmare is a very serious flaw and should be addressed as soon as possible. The vulnerability has not yet been addressed, so administrators of affected systems are encouraged to disable the Print Spooler service, especially on domain controller systems.
Hacking groups, mainly ransomware operators, could exploit this flaw to compromise enterprise networks because obtaining access credentials to domains with reduced privileges is a relatively simple task for more experienced hackers. Detailed information about mitigation mechanisms is available on official Microsoft platforms.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











