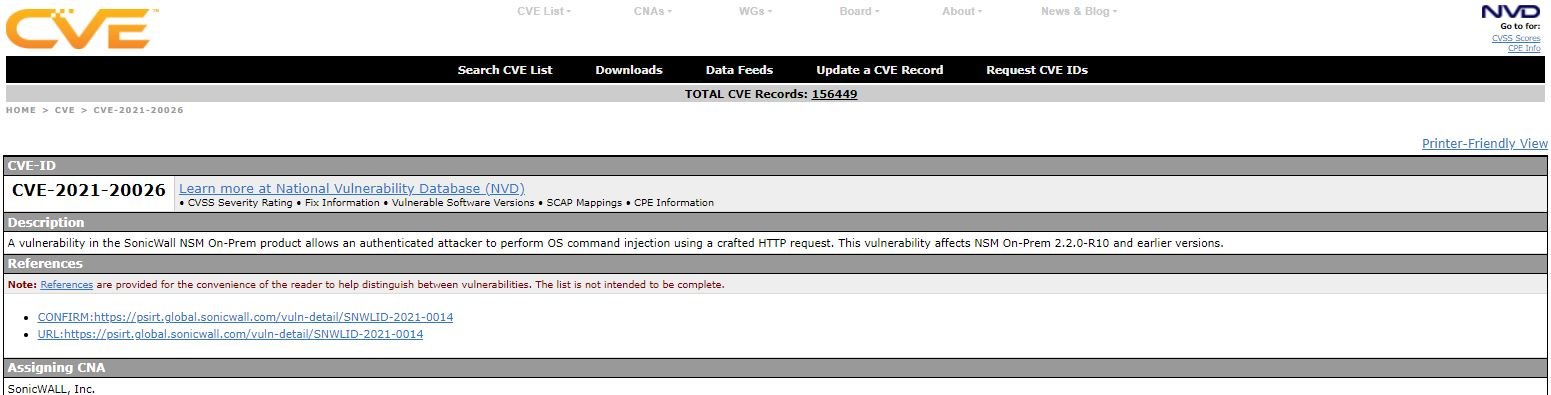
Nikita Abramov, a researcher at security firm Positive Technologies, issued an alert regarding CVE-2021-20026, a command injection vulnerability in Network Security Manager (NSM) solutions, produced by SonicWall. Updates to address this flaw were released in late May.
At that time, the flaw received a score of 8.8/10 on the Common Vulnerability Scoring System (CVSS) scale. An authenticated threat actor could exploit the vulnerability to inject operating system commands by sending specially crafted requests.
In its report, the company mentions, “We have addressed a severe vulnerability in a specific product that resides only in local NSM implementations. SaaS versions are not affected by this command injection vulnerability and its execution allows the execution of commands on the operating system with root user privileges.”
For its part, Abramov assures that the flaw exists due to the incorrect validation of the data entered by the user to the operating system. The researcher mentions that a least-privilege threat actor in NSM could exploit the vulnerability.
“A successful attack requires authorization on NSM with a minimum level of privilege. SonicWall NSM enables the centralized management of hundreds of devices, so tampering with this system can negatively affect an organization’s ability to work, to the point of completely disrupting its protection system and stopping dozens of critical processes,” abramov concludes.
As usual, users of affected deployments are invited to address the flaws with the installation of security patches released by SonicWall. At the moment, no alternative mitigation methods are known.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











