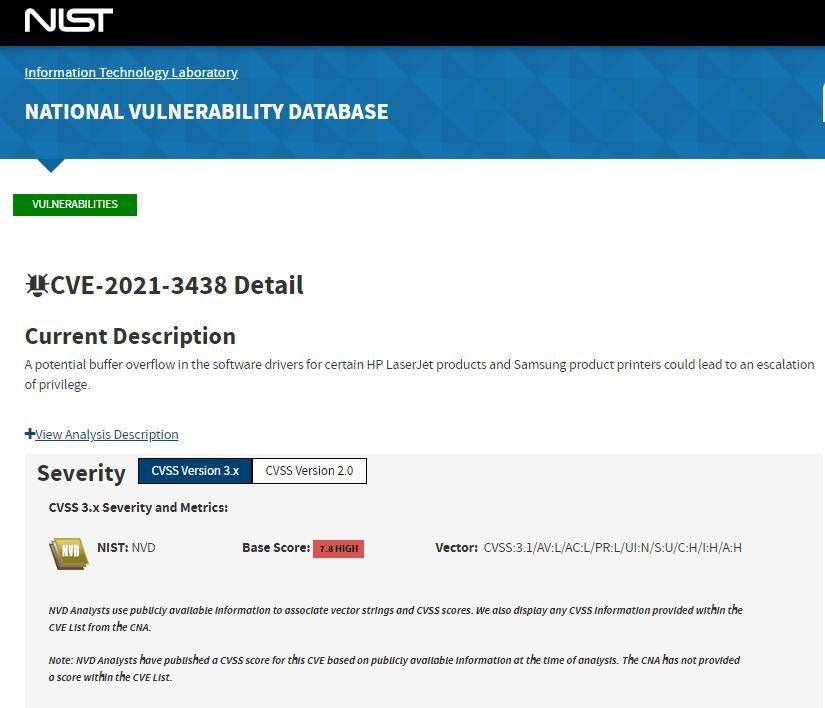
HP security teams announced the fix of a critical vulnerability in a print driver that remained unnoticed for more than 15 years. The flaw was tracked as CVE-2021-3438 and received a score of 8.8/10 on the Common Vulnerability Scoring System (CVSS) scale.
The vulnerability was described as a potential buffer overflow in software drivers for certain HP LaserJet products and Samsung product printers that could lead to privilege escalation. A security report published by SentinelLabs mentions that some HP, Xerox and Samsung printer models could contain the vulnerable software, distributed worldwide since 2005.
The vulnerable driver was identified as SSPORT.SYS, which is installed and activated automatically regardless of whether the printer is wireless or wired. It should be clarified that the Windows operating system also loads this driver automatically when the device boots: “Given its characteristics, this driver is an ideal target for hackers, as it will always load into the operating system even if a printer is not connected,” the report states.
To be precise, the vulnerable function of the driver is the process of accepting data without the validation of the size parameter. A threat actor could invade the driver buffer to elevate its privileges to a SYSTEM account and execute kernel-mode code to perform arbitrary actions.
While the researchers found that the flaw can be exploited, the SentinelLabs report does not include a proof of concept (PoC) exploit or a more detailed description of the attack.
Researchers reported the flaw last February, so HP released a security patch in mid-May. The company mentions that no exploits have been detected in real scenarios, although they acknowledge that the affected models include those produced by manufacturers such as Samsung, HP, MultiXpress and Samsung Xpress.
Finally, the company asked users of affected deployments to update as soon as possible in order to mitigate the risk of exploitation.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











