Tor is the most famous web browser which provides anonymity/ privacy over the internet. Many companies/ whistle blowers uses TOR for working anonymously. Some Hacking groups also uses TOR services for spreading malware’s, viruses. According to ethical hacking researcher of international institute of cyber security Earlier we have shown that how you share files on TOR network.
Today we will show you that how you can redirect your web traffic using tor proxies.We will use TOR-Router, a project from github. TOR router redirects all files under web traffic
- For testing we will use Kali Linux 2018.4 amd64. Open terminal type git clone https://github.com/Edu4rdSHL/tor-router.git
- Before installing ensure that TOR is installed. For that type sudo apt-get update & sudo apt-get install tor
- Type cd tor-router
- Type sudo bash install.sh && cd files
- After installing tor, must configure that following lines are written in the end.
- For that type nano /etc/tor/torrc & copy the below lines. These are lines are the configuration of TOR browser.
# Seting up TOR transparent proxy for tor-router
VirtualAddrNetwork 10.192.0.0/10
AutomapHostsOnResolve 1
TransPort 9040
DNSPort 5353- After configuring restart the tor service.
- Open another terminal type cd /home/iicybersecurity/Downloads/tor-router/files && type sudo ./tor-router
- Now the tor service has started.
- For checking if the tor is configured to redirect traffic. Open https://check.torproject.org link from Mozilla firefox web browser.
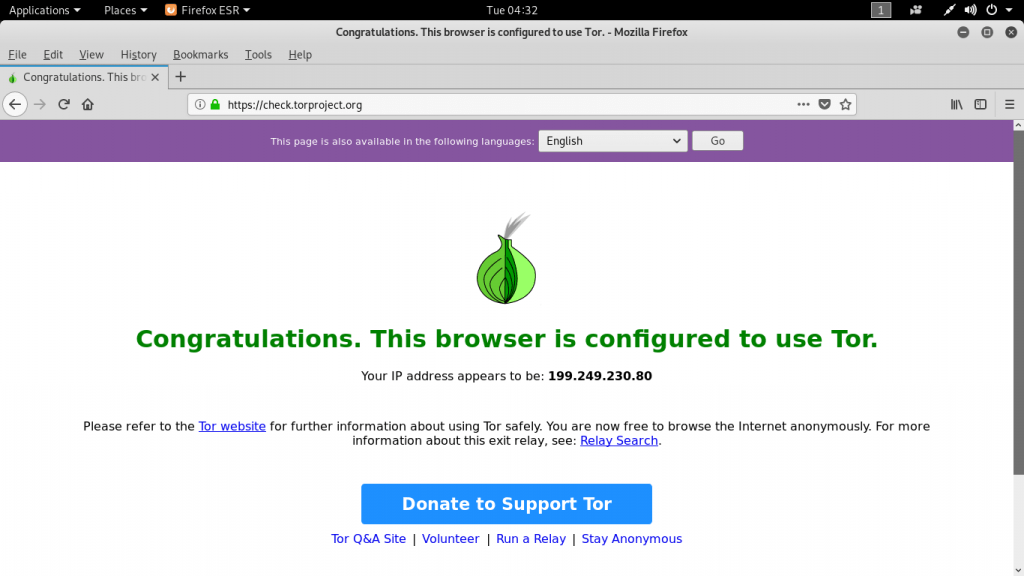
- Above you can see that this web browser is configured to use tor. For checking the dns leak test go to : https://dnsleaktest.com/
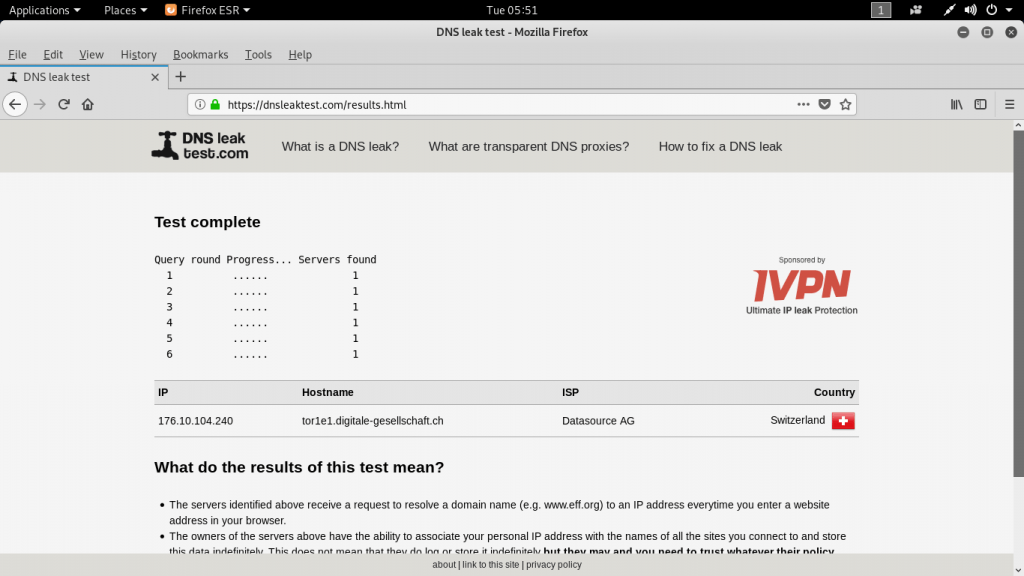
- In DNS leak, it showing its current location in Switzerland. For final configuration we will check through what is my ip address website.
- Go to : whatsismyipaddress.com
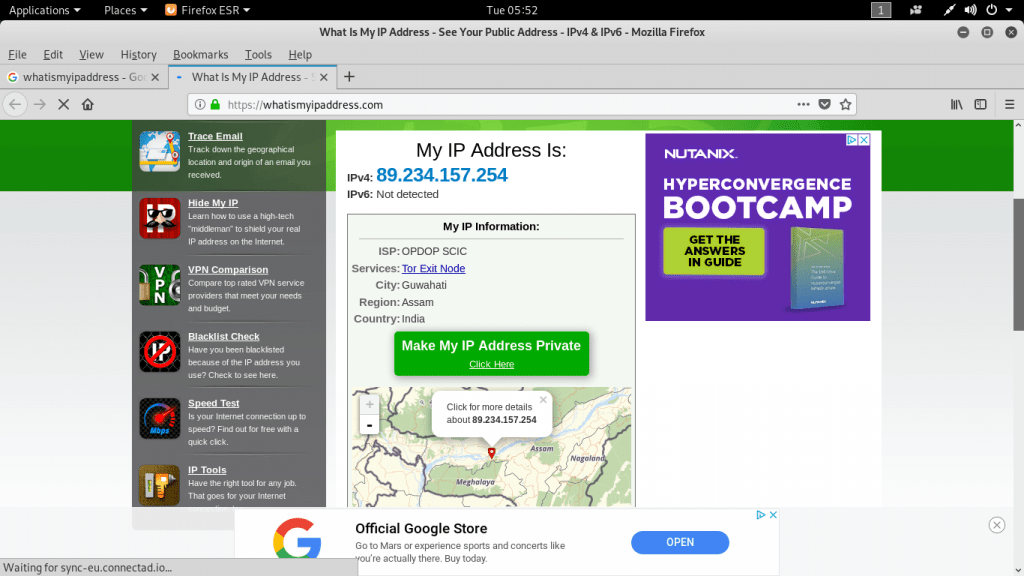
- You can see it current location is in Guwahati (Assam) with Tor exit node.

Cyber Security Researcher. Information security specialist, currently working as risk infrastructure specialist & investigator. He is a cyber-security researcher with over 25 years of experience. He has served with the Intelligence Agency as a Senior Intelligence Officer. He has also worked with Google and Citrix in development of cyber security solutions. He has aided the government and many federal agencies in thwarting many cyber crimes. He has been writing for us in his free time since last 5 years.











