A recent report claims that the vulnerability affecting Checkbox Survey, a tool ASP.NET to add survey functionality to websites, was exploited by a hacking group sponsored by the Chinese government in a campaign against public and private organizations in the U.S. The report, prepared by security firm Sygnia, does not expressly mention the Chinese government, although it notes that the tactics and procedures employed in this campaign have previously been attributed to actors in the Asian giant.
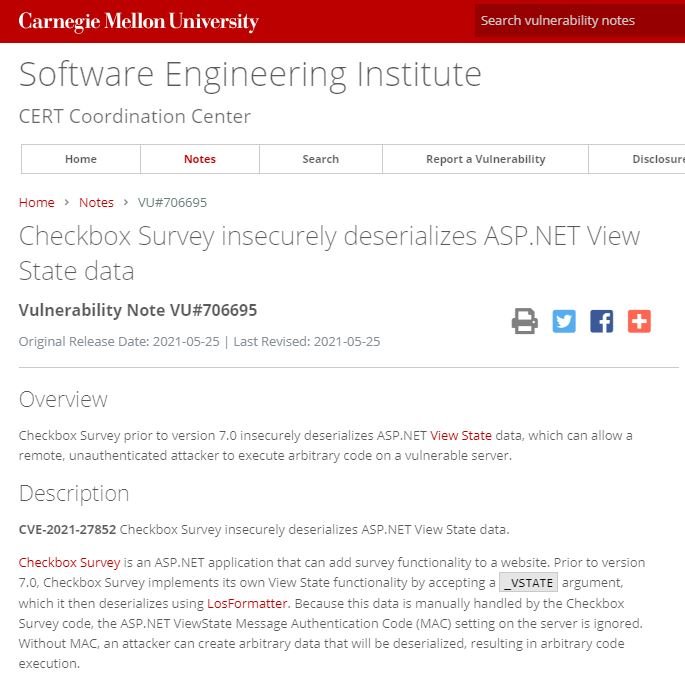
The vulnerability in question was identified as CVE-2021-27852 and is described as a code execution flaw due to deserialization impacting version 6 of checkbox survey. The flaw can be exploited remotely by unauthenticated threat actors. Version 7 of the tool is completely secure, although users should consider that older versions will not receive updates.
Checkbox Survey mentions that its solutions are employed by companies around the world, including government organizations such as NASA, NATO, the U.S. military, the State Department and even the Nuclear Regulatory Commission.
As mentioned at the outset, Sygnia found multiple links between this campaign and an attack on private industry and government organisations in Australia detected in 2020. At first there was no suspicion about those responsible for the attack, although this changed with subsequent investigations.
Sygnia has found similarities between the malware used in australia attacks and this recent campaign against Checkbox Survey. However, experts mention that the incident in Australia was more far-reaching and consists of other tactics and procedures.
The researchers identified the attackers as TG1021 or Praying Mantis, noting that this is a group with advanced capabilities and employing deserialization exploits targeting vulnerable Windows IIS servers. The malware employed by these hackers contains custom tools designed specifically for IIS servers, plus a backdoor and multiple post-exploit modules for the deployment of multiple hacking tasks.
Sygnia experts described this malware as a “volatile development” that must be loaded into the memory of the compromised device in an effort to try to remove its traces. The exploitation campaign against Checkbox Survey is still active, so affected users are advised to upgrade to the secure version of this tool in order to mitigate the risk of exploitation.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











