Cybersecurity specialists found a critical vulnerability in Moodle, a popular online learning platform. According to the report, successful exploitation of this flaw would allow access to students’ information and exam results. Moodle is currently employed by more than 190 thousand organizations worldwide, including companies and educational institutions such as universities or colleges.
The flaw was described as a PHP object injection bug in the Shibboleth authentication module, which would allow unauthenticated threat actors to execute remote code execution (RCE) attacks. This condition would also allow hackers to access any information held on the compromised server, including personal data.
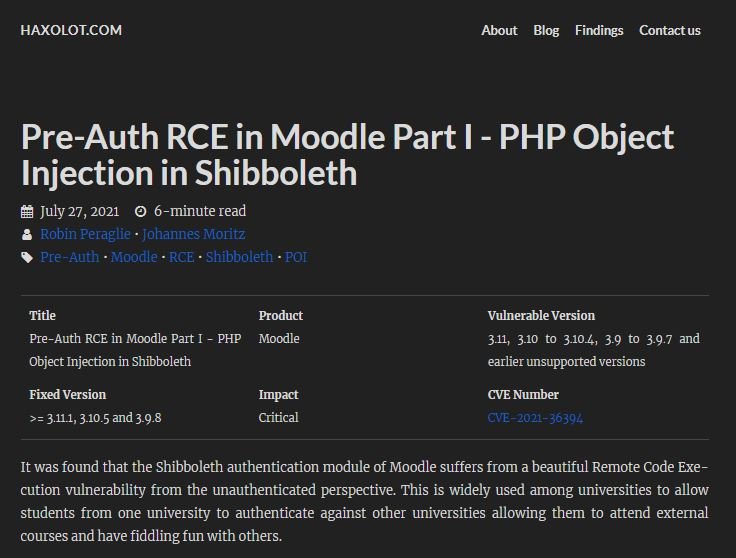
The flaw was reported by Robin Peraglie and Johannes Moritz, pentesting specialists who had previously found other faults in Moodle. Moritz mentions that the flaw only resides on the Moodle LMS server, which has Shibboleth authentication enabled; this module is disabled by default, so enabling it can represent serious inconveniences for organizations that use Moodle, as it can be exposed to arbitrary code execution.
“Such an attack would result in a total server compromise, in addition to exposing the leak of user data. A malicious user could also abuse these features to gain read/write access to their own exams,” Moritz adds. The researcher adds that this is a relatively easy flaw to exploit, as there is a wide availability of information on websites with Shibboleth enabled on the Internet.
After reporting the problem and after a lengthy disclosure process, the flaw was finally addressed. This process required four months of evaluation and failures, so Moritz believes this flaw was not treated with the required priority. Finally, the researcher revealed the detection of a second critical flaw in Moodle’s pre-authentication process. This flaw has already been corrected, although the information related to this error will be published when the company deems it safe.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











