Security issues in the GNU C library (gblic) can be disastrous for Linux users. An example of this is CVE-2021-33574, a vulnerability that would have allowed threat actors to cause all sorts of flaws in Linux applications. While the flaw was addressed, the implementation of this fix led to the discovery of CVE-2021-38604, an even more dangerous vulnerability.
In analyzing the aforementioned patch, researcher Nikita Popov discovered that it was possible to lead to a segmentation scenario within the affected library, which could lead to a much easier to exploit denial of service (DoS) condition than the initially fixed vulnerability.
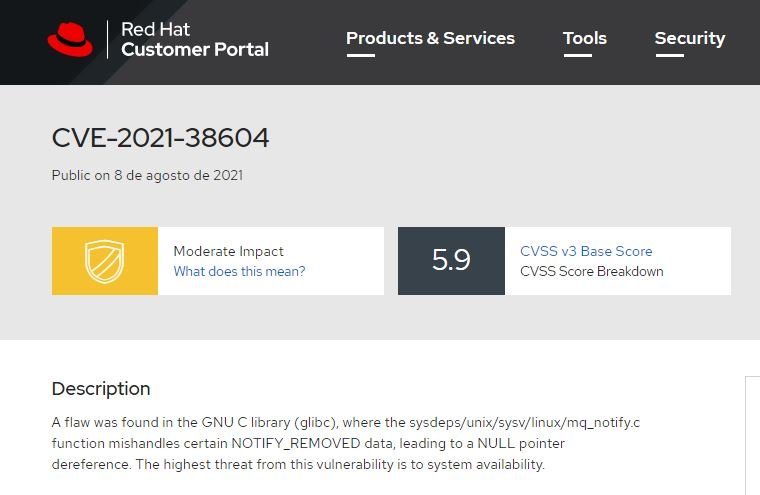
According to a Red Hat report, the flaw received a score of 7.5/10 according to the Common Vulnerability Scoring System (CVSS) and can be exploited by users without high privileges, so it is considered a high-severity flaw. On the other hand, Popov believes that this flaw could affect all Linux applications, including interpreters of other languages such as Python or PHP, as they are related to glibc.
The researcher adds that this problem was found during a routine analysis, when it was discovered that null pointers could be passed in certain situations. To be precise, this problem lies in the ‘mq_’ family of functions, which provide POSIX-compliant message queuing API capabilities, something shared by all Linux language interpreters.
Popov encountered two scenarios in which the Linux kernel might use the message NOTIFY_REMOVED when passing thread attributes copied to the data.attr field. Unfortunately, a host application can pass a null value there if it wants glibc to generate a thread with default attributes. In this case, glibc would remove the reference from a NULL pointer in pthread_attr_destroy, blocking all system processes.
Linux distribution developers are discussing the best possible way to address this issue, ironically generated by a security update. In the meantime, users of affected deployments are encouraged to upgrade to the latest version of glibc.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











