Project Zero, Google’s cybersecurity unit, published research detailing its analysis of the Windows firewall and AppContainer, Microsoft’s runtime environment that restricts applications so that security risks can be avoided before installing new software.
In its report, Project Zero points to the detection of a severe vulnerability in AppContainer that Microsoft had chosen not to address, though the new reports appear to have caused the company to change its mind.
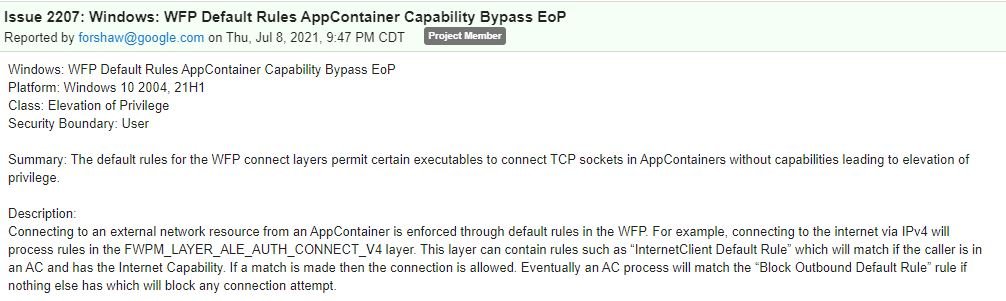
According to James Forshaw of Project Zero, there is a way to circumvent the restrictions enforced by AppContainer, which would allow threat actors to access services on localhost and Intranet resources: “The default rules in this tool allow certain executables to connect TCO sockets to AppContainers, which could lead to privilege escalation”, notes the report.
The researcher reported its findings to Microsoft in July, although at the time the company mentioned that the vulnerability would not be fixed because a successful attack would necessarily require the prior compromise of an AppContainer implementation.
In response, Project Zero revealed the details of this vulnerability, evading the rule that these reports must wait 90 days after reporting to the manufacturer of the affected product. This measure allows members of the cybersecurity community to discuss the manufacturer’s decision and sometimes develop functional workarounds.
Almost simultaneously with the Project Zero report, Microsoft announced that it would continue to work to address the vulnerability. At the moment it is unknown why the company changed its mind, although more details are expected to be revealed as soon as the flaw is addressed and the security patch is available.
While it seems somewhat strange, it’s common practice for Google Project Zero to publicly reveal reports about flaws that Microsoft and other tech companies can’t or choose not to update.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











