A recent investigation by security firm SecureList discovered a mod for WhatsApp that could hide a dangerous variant of malware. The mod, identified as FMWhatsApp v16.80.0, hides the Triada Trojan, used by cybercriminal groups to download additional modules to the affected system, display malvertising and even add the affected user to subscription services without authorization.
Very popular in the world of video games, a “mod” is a software variant designed to alter the factory settings of another software sample. In this case, the WhatsApp mod allows users to customize the app’s interface and is available on third-party app stores and disputable websites.
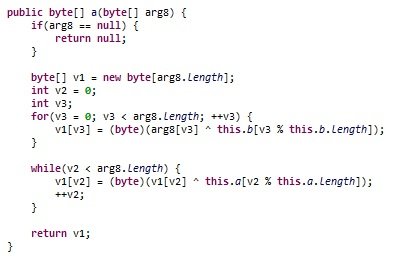
After it is downloaded and installed on the affected device, the Trojan begins to collect unique system identifiers, including device IDs, subscriber IDs, MAC addresses, plus the package name of the application where they are deployed. The information they collect is sent to a remote server controlled by hackers to register the device.
By analyzing the statistics on the files downloaded by FMWhatsapp, SecureList experts were able to find more than one malware variant, including:
- Trojan-Downloader.AndroidOS.Agent.ic: For downloading and running other malicious modules
- Trojan-Downloader.AndroidOS.Gapac.e: For the appearance of full-screen ads
- Trojan-Downloader.AndroidOS.Helper.a: Download and run the xHelper Trojan installation module
- Trojan.AndroidOS.MobOk.i: Arbitrary subscription to paid services
So far, researchers have detected at least 33 thousand attacks related to this and other WhatsApp mods, making it a problem that has grown steadily. Mod developers know how easy it is to get involved in victims’ devices.
Another fundamental aspect to consider is that, despite the dangerousness of this malware, it should be the victim who authorizes all these malicious actions through the installation of the mod. That is why the main security recommendation is not to install software downloaded from unknown websites or from unofficial stores, since this is the main method to install malware on an affected smartphone.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











