Hewlett Packard Enterprise (HPE) security teams report a severe vulnerability in Sudo, the open source program used by the Aruba AirWave solution. According to the report, successful exploitation of the flaw would allow any local user with least privileges to obtain root privileges on compromised hosts.
Tracked as CVE-2021-3156, the flaw was reported by Qualys researchers in early 2021 and would be present in millions of active devices. In this regard, HPE concluded that the vulnerability could be chained with other cyberattacks in order to escalate privileges on the affected systems.
As some users will recall, Sudo is a program used by other platforms in order to delegate authority to grant certain users certain capabilities in a specific system. Mehul Revankar, a researcher at Qualys, described the vulnerability as “the Sudo bug with the greatest potential impact ever detected,” adding that the flaw had been present for at least 10 years.
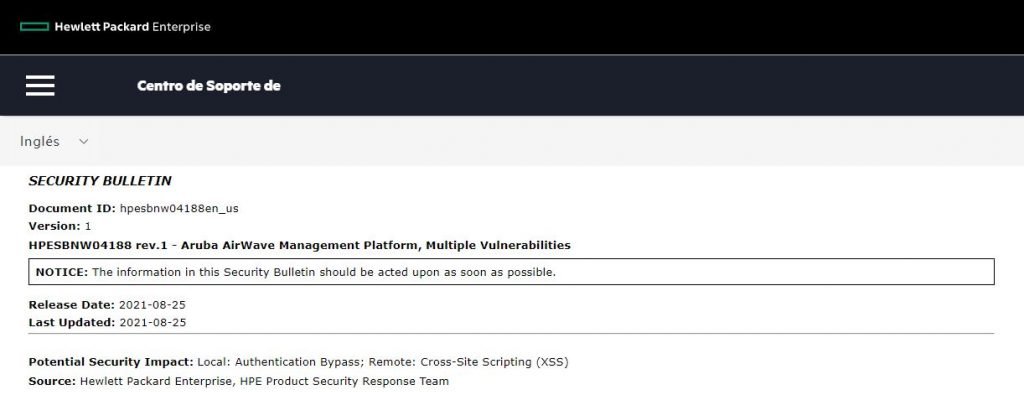
Although it received the report months ago, HPE revealed the flaw just last week, noting that it affects all versions of its AirWave management platform prior to v8.2.13.0, released a couple of months ago: “The vulnerability could allow an attacker with access to Sudo to execute commands or binaries with root privileges.”
Qualys researchers dubbed this flaw “Baron Samedit,” noting that its existence dates back to 2011. Although at first it was believed that the flaw only affected Linux and BSD systems, little by little its presence was confirmed in other implementations, including HPE solutions.
Finally, although HPE is the latest company to confirm the presence of this flaw in its products, experts believe that it will not be the last; even so, it is difficult to measure the approximate extent of potential large-scale exploitation.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











