Cybersecurity specialists report the detection of a remote code execution (RCE) vulnerability in Visual Studio Code Remote Development, a platform that allows users to adopt a container, virtual machine or Windows Subsystem for Linux (WSL) as a full-featured development environment.
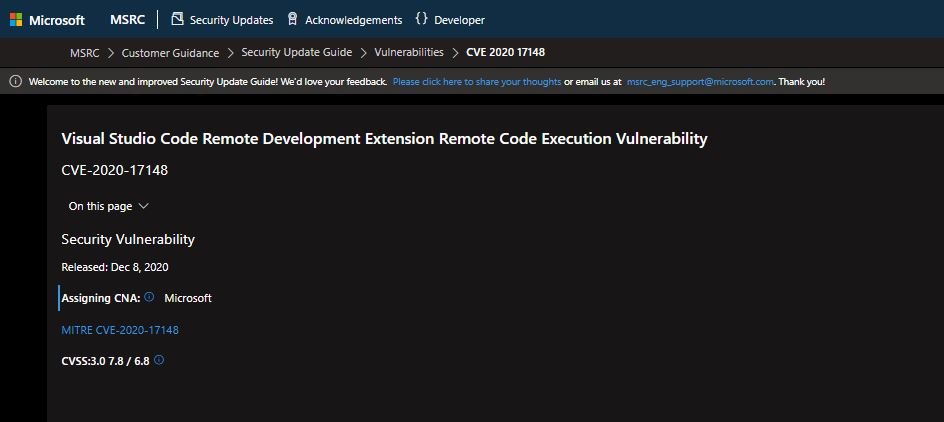
The report, prepared by the cybersecurity firm Shielder, notes that version 1.50 of this software is unable to disinfect the host field passed as an argument of the ssh command, which would allow unauthenticated remote hackers to abuse the flaw to inject a ProxyCommand option, resulting in remote code execution. The flaw was tracked as CVE-2020-17148; its score according to the Common Vulnerability Scoring System (CVSS) has not been yet determined.
On the other hand, a security alert published by Microsoft mentions that attackers would have to trick a user with this extension installed to click on a specially designed link and carry out the attack: “Successful exploitation can only occur under these circumstances,” says the security alert.
The argument injection required for the attack resides in the “Remote-SSH” extension, which is installed together with Remote Development.
Researcher Abdel Adim Oisfi published a proof of concept (PoC) to demonstrate the possibility of exploitation in a relatively simple process and which includes the steps listed below:
- Install Visual Studio Code
- Install the “Remote Development” extension
- Launch a browser of your choice
- Go to the following URL:
vscode://vscode-remote/ssh-remote+-oProxyCommand=C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -c msg %username% command_injection” “a@127.0.0.1+/a
- Confirm to open VSCode
- Choose an operating system, preferably randomly
- Identify the pop-up window run by Powershell with the message “command_injection”
The attack also works on Linux and MacOS; users just have to edit the ProxyCommand. Microsoft fixed the error with the release of Visual Studio Code Remote Development Extension v1.51 or higher, so affected users should update as soon as possible.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











