Citrix Hypervisor is an industry leading platform for cost-effective desktop, server, and cloud virtualization infrastructures. Citrix Hypervisor enables organizations of any size or type to consolidate and transform compute resources into virtual workloads for today’s data center requirements. Citrix has released hotfix to patch important Information disclosure, Incomplete cleanup and Race condition vulnerabilities.
1) Information disclosure
CVE-ID: CVE-2022-21123, CVE-2022-21125, CVE-2022-21166
Description
The vulnerability allows a threat actor to take control of confidential information. The vulnerability exists in Intel processors due to excessive data output when DirectPath I/O (PCI-Passthrough) is utilized. A local or remote threat actor with administrative access to a virtual machine that has an attached DirectPath I/O (PCI-Passthrough) device can obtain information stored in physical memory about the hypervisor or other virtual machines that reside on the same host.
2) Incomplete cleanup
CVE-ID: CVE-2022-21127
Description
The vulnerability allows a local threat actor to gain access to sensitive information on the system.
The vulnerability exists due to incomplete cleanup in specific special register read operations. A local threat actor can enable information disclosure.
3) Race condition
CVE-ID: CVE-2022-26362
Description
The vulnerability allows a remote threat actor to execute arbitrary code on the target system.
The vulnerability exists due to race condition in typeref acquisition Xen. A remote threat actor can execute arbitrary code on the target system.
Vulnerable software versions
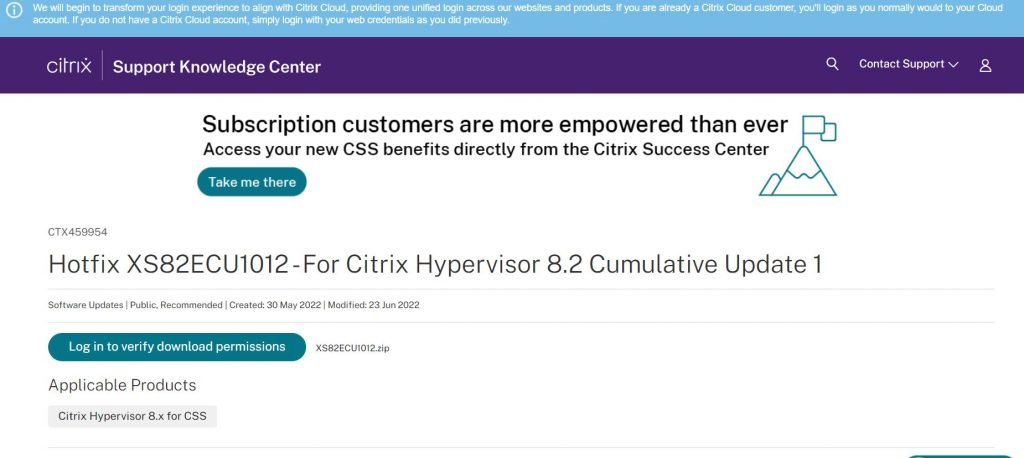
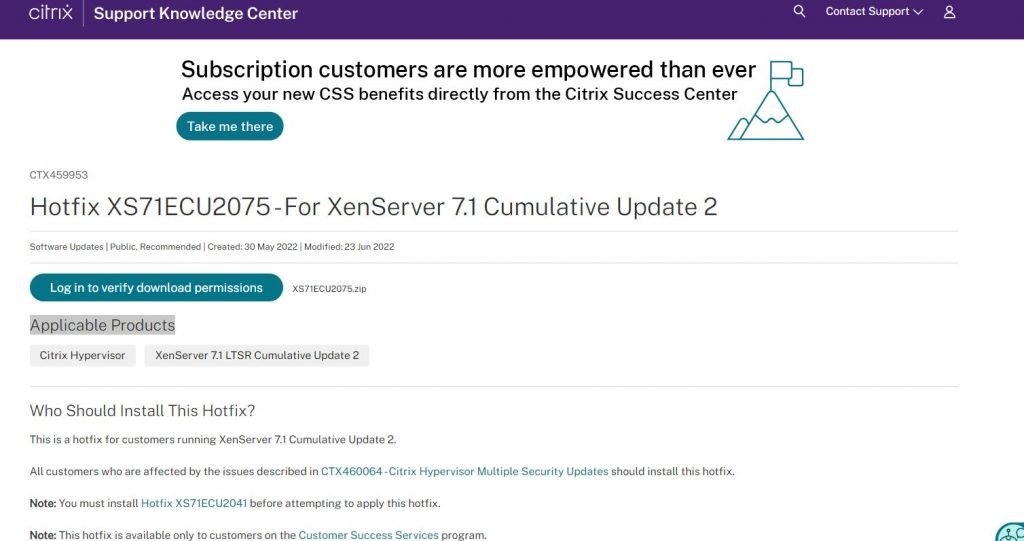
Citrix Hypervisor: 7.1 CU2 – 8.2 CU1
Mitigation
Install hotfix from the citrix’s website.Customers should use either XenCenter or the Citrix Hypervisor Command Line Interface (CLI) to apply this hotfix. As with any software update, back up your data before applying this update. Citrix recommends updating all servers within a pool sequentially. Upgrading of servers should be scheduled to minimize the amount of time the pool runs in a “mixed state” where some servers are upgraded and some are not. Running a mixed pool of updated and non-updated servers for general operation is not supported.
Installing the Hotfix by using XenCenter
Choose an Installation Mechanism
There are three mechanisms to install a hotfix:
- Automated Updates
- Download update from Citrix
- Select update or Supplemental pack from disk
The Automated Updates feature is available for Citrix Hypervisor Premium Edition customers, or to those who have access to XenServer through their Citrix Virtual Apps and Desktops entitlement. For information about installing a hotfix using the Automated Updates feature, see the Applying Automated Updates in the Citrix Hypervisor documentation.

Cyber Security Specialist with 18+ years of industry experience . Worked on the projects with AT&T, Citrix, Google, Conexant, IPolicy Networks (Tech Mahindra) and HFCL. Constantly keeping world update on the happening in Cyber Security Area.











