Rolling-PWN attack vulnerability CVE-2021-46145 affecting all Honda cars models that exist from the year 2012 up to the year 2022. This vulnerability allows anyone to permanently open the car door or even start the car engine remotely.
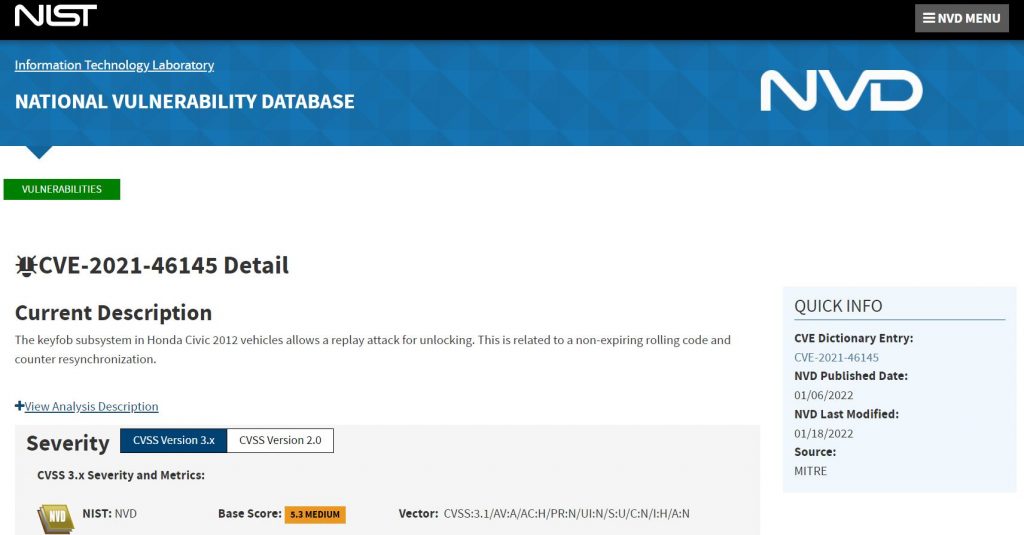
The Rolling-PWN bug is a critical vulnerability. Researchers found it in a vulnerable version of the rolling codes mechanism, which is implemented in all Honda vehicles. A rolling code system in keyless entry systems is to prevent replay attacks. After each keyfob button is pressed the rolling codes synchronizing counter is increased. Nevertheless, the automobile receiver will accept a sliding window of codes, to avoid unintentional key pressed. By sending the commands in a consecutive sequence to the Honda vehicles, it will be resynchronizing the counter. Once counter resynced, commands from the previous cycle of the counter worked again. Therefore, those commands can be used later to unlock the car at will.
A team of security Researchers Kevin2600 and Wesley Li from Star-V Lab independently discovered this vulnerability. Kevin2600 explained that the attack relies on a vulnerability that allows a attacker using a software defined radio to capture the code that the car owner uses to unlock the vehicle, and then replay it so that the attacker can unlock the vehicle as well. In some cases the attack can be done remotely from 30 meters away.
The vulnerability affects all Honda vehicles currently existing on the market.
· Honda Civic
· Honda X-RV
· Honda C-RV
· Honda Accord
· Honda Odyssey
· Honda Inspire
· Honda Fit
· Honda Civic
· Honda VE-1
· Honda Breeze
Although the main targets for the research are Honda Automobiles. But researchers believe that his vulnerability also applies to other car manufacturers. They will release more details in the future.
Earlier some other researchers have discovered CVE-2022-27254 that also affected Honda vehicles. Based on the description “The remote keyless system on Honda HR-V 2017 cars sends the same RF signal for each car unlock request, which might allow a replay attack”. Which attacker can record and and replays it later to cause the car door to lock or unlock.
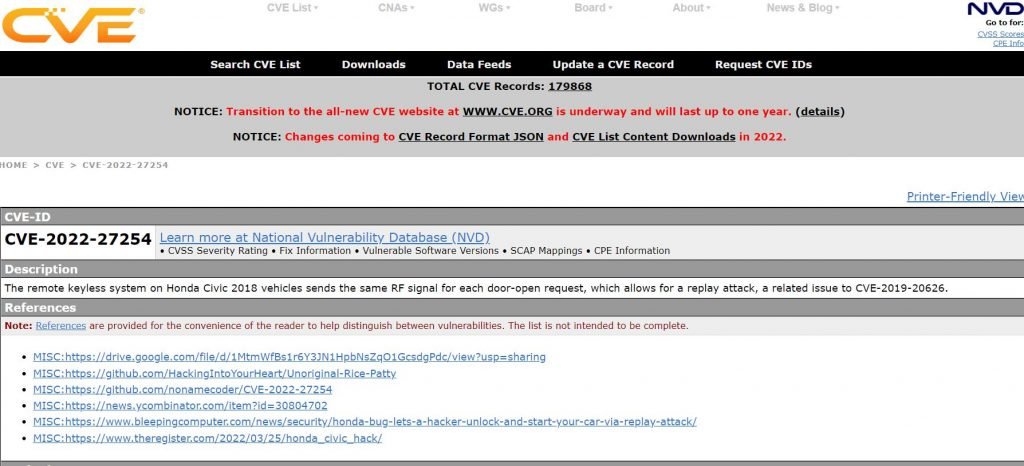
However, most modern vehicles including Honda Automobiles implemented the proprietary rolling codes mechanism, which fixes CVE-2022-27254.
Mitigation
The common solution requires us to take the car back to the dealership. But the recommended mitigation strategy is to upgrade the vulnerable BCM firmware through Over-the-Air (OTA) Updates if feasible. Some old vehicles may not support OTA.
Researchers haven’t got any reply from Honda company so there is no solution to fix this vulnerability as of now.

Cyber Security Specialist with 18+ years of industry experience . Worked on the projects with AT&T, Citrix, Google, Conexant, IPolicy Networks (Tech Mahindra) and HFCL. Constantly keeping world update on the happening in Cyber Security Area.











