The Dirty Cred Linux kernel attack was unveiled at the Black Hat security conference last week.
The CVE-2022-0847 vulnerability was found by PhD student Zhenpeng Lin and his colleagues, who attempted to exploit the Linux kernel similarly to the classic Dirty Pipe vulnerability but using different strategies.
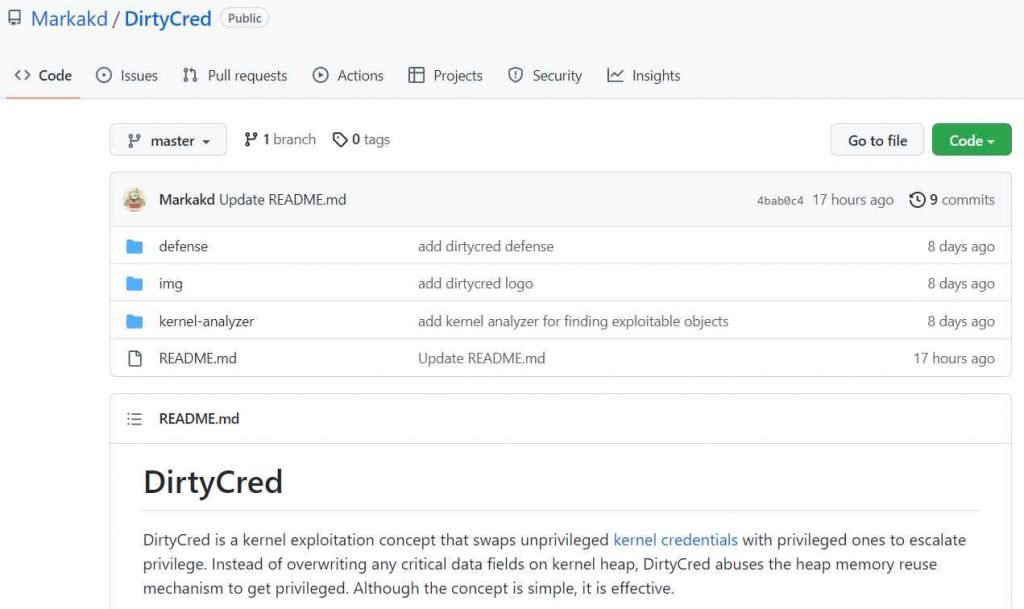
A kernel exploitation concept called “DirtyCred” swaps out non-privileged kernel credentials for privileged ones in order to elevate power. In order to gain privileges, DirtyCred takes advantage of the heap memory reuse mechanism rather than overwriting any important data fields on the kernel heap. Any read-only files that are affected by kernel version 5.8 or above are overwritten.
On systems vulnerable to both a recently published vulnerability (CVE-2021-4154) and a previously unknown weakness (CVE-2022-2588), Lin’s team found a way to swap Linux Kernel credentials, and they anticipate adding additional suitable CVEs in the future. On GitHub, there is a public POC (proof of concept) that provides a strong protection against the assault.
The researchers characterized their attack scenario as a general approach that may be used with Android and containers.
Using the same attack code, Lin presented a demo on Twitter showing how the strategy can be used to elevate a low-privileged user on two distinct operating systems, such as Centos 8 and Ubuntu.
Protection against DirtyCred
Despite the fact that the POC is already functioning under some circumstances, such as a particular vulnerability, it should be emphasized that it is still in development. The Linux kernel contains a fix for CVE-2021-4154, but according to the researchers, “the attack works on most Centos 8 kernels higher than Linux-4.18.0-305.el8 and most Ubuntu 20 kernels higher than 5.4.0-87.98 and 5.11.0-37.41.”
The researchers advocate segregating privileged credentials from unprivileged ones using virtual memory to prevent cross-cache attacks since objects are segregated based on their type rather than their rights.

Cyber Security Researcher. Information security specialist, currently working as risk infrastructure specialist & investigator. He is a cyber-security researcher with over 25 years of experience. He has served with the Intelligence Agency as a Senior Intelligence Officer. He has also worked with Google and Citrix in development of cyber security solutions. He has aided the government and many federal agencies in thwarting many cyber crimes. He has been writing for us in his free time since last 5 years.











