Microsoft has been informed about the incorrectly configured Microsoft endpoint by security experts at SOCRadar. This results in unauthorized access to some business transaction data pertaining to exchanges between Microsoft and potential clients, such as the preparation for and future deployment of Microsoft services. Papers that may include intellectual property are also included in the breach, along with Proof-of-Execution (PoE) and Statement of Work (SoW) documents, user data, product orders and offers, project information, and PII (Personally Identifiable Information) data. The client data was exposed in the public buckets, and among them, six sizable ones included details for more than 150,000 businesses across 123 nations.
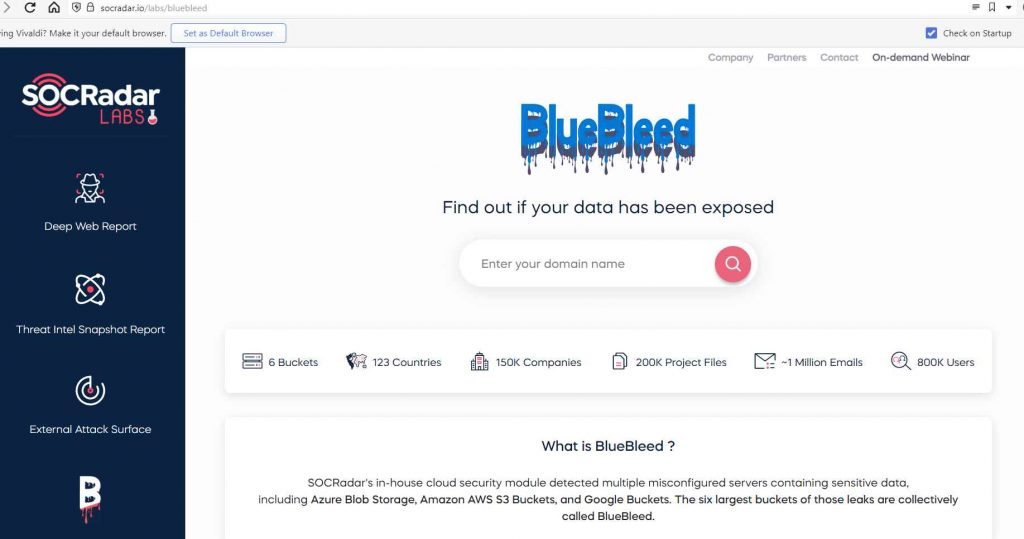
The breach was dubbed BlueBleed by SOCRadar, a phrase used to describe the sensitive data that was collectively spilled by six incorrectly configured buckets.
The SOCRadar reports that the misconfigured server, SQLServer databases, and other Microsoft files exposed 2.4 TB of private data. Files with dates ranging from 2017 to August 2022 are among the exposed data.
According to SOCRadar, the breach, known as BlueBleed Part I, contains sensitive information from more than 65,000 firms in 111 countries. This information comprises more than 335,000 emails, 133,000 projects, and 548,000 exposed users in the dumps to far.
In the incorrectly configured bucket, the exposed files consist of; invoices, product orders, product offers, POE documents, SOW papers, project information ,Customer-signed contracts, POC (Proof of Concept) projects, client emails (as well as .EML files), client stock levels and the pricing list for their products, Internal feedback for clients (High risk etc.), Customer asset records, sales methods, and Partner ecosystem details.
Companies may use the BlueBleed search tool, which SOCRadar released, to discover whether any of the BlueBleed leaks had an impact on their company names.
Microsoft laments SOCRadar’s decision to make a “search tool” available to the public, claiming it is not in the best interest of protecting consumer privacy or security and may put them at undue danger.
In the blog entry, Microsoft stated:
“Our investigation revealed no evidence that any systems or customer accounts had been accessed. The impacted consumers have been immediately informed by us.
“The problem was not the consequence of a security vulnerability, but rather an unintended configuration error on an endpoint that is not in use throughout the Microsoft ecosystem.
“No evidence of corrupted customer accounts or systems was identified throughout our examination. The impacted clients have already been informed immediately.”
“The problem wasn’t the consequence of a security flaw, but rather an unintended setup error on an endpoint that wasn’t being utilized by the whole Microsoft ecosystem.
To further prevent this kind of misconfiguration, we are striving to strengthen our procedures. We are also carrying out more due diligence to check the security of all Microsoft endpoints.”


Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











