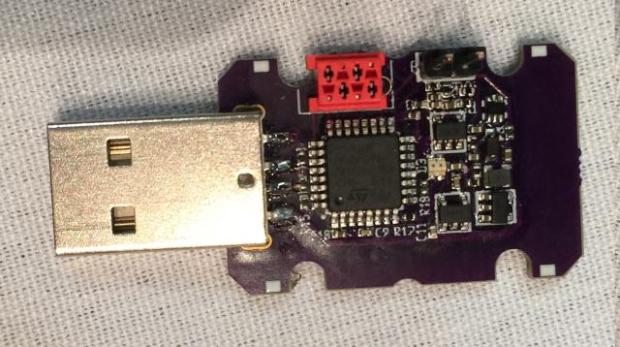
ChaosKey: This is a hardware True Random Number Generator that attaches via USB.
This is a hardware True Random Number Generator that attaches via USB. Version 0.3 This one uses the better noise source coupled with an op amp that provides 2MHz ofRead More →