12 Best WiFi Hacking Apps For Android Smartphones | 2017 Edition
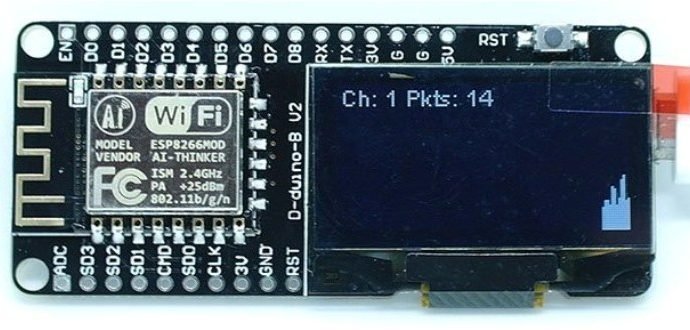
Hacking WiFi networks is an important part of learning the subtleties of ethical hacking and penetration testing. This also gives rise to the need for some quality WiFi hacking appsRead More →