Iranian hackers are back with the MACDOWNLOADER MAC malware
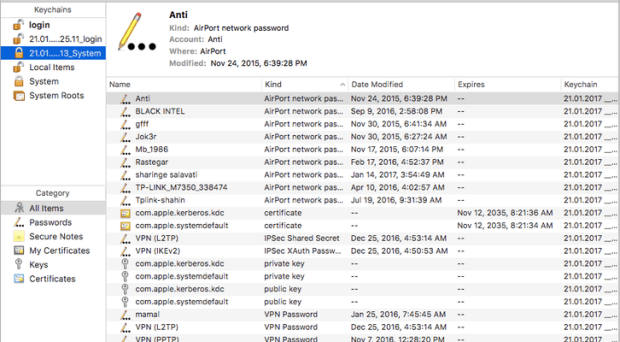
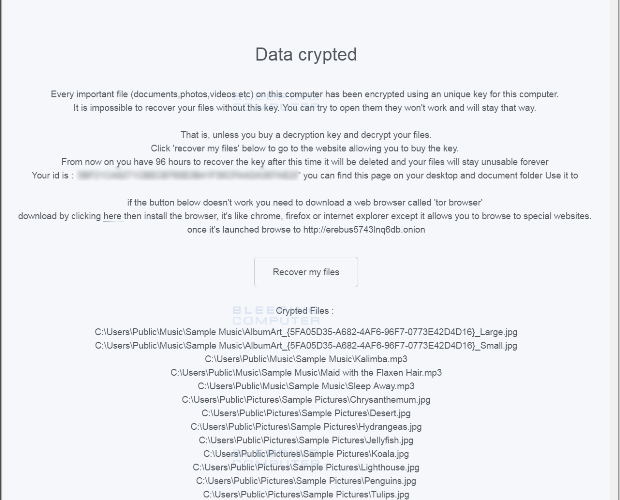
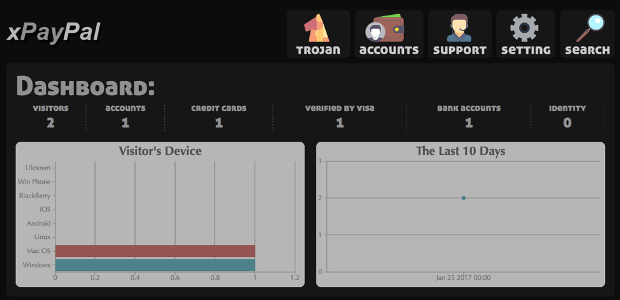
An Iranian espionage group has been using an unsophisticated strain of malware, dubbed MacDownloader, to steal credentials and other data from Mac users. A cyber espionage group linked to theRead More →