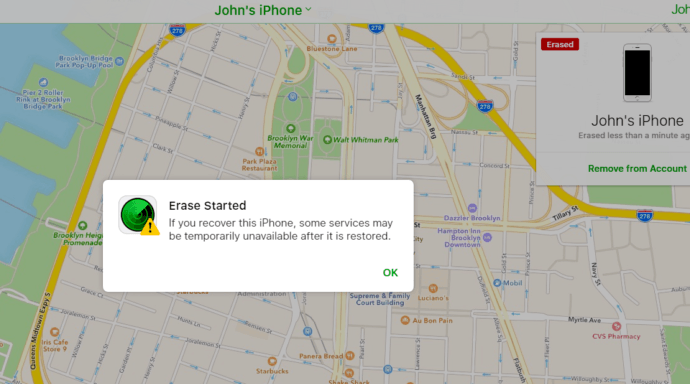
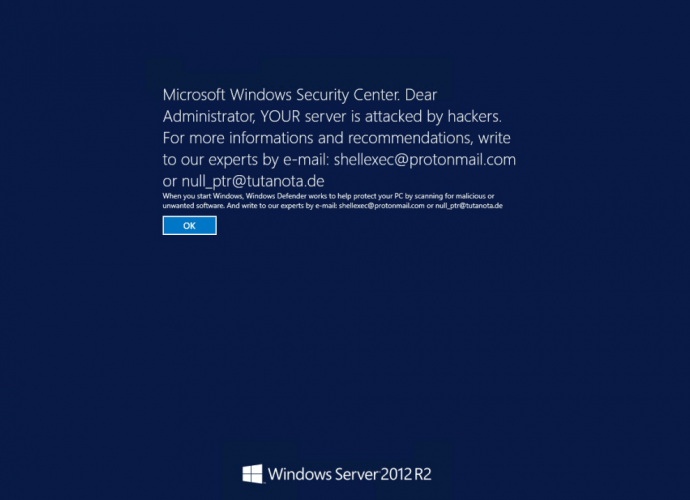
Clinton campaign chief’s iPhone was hacked and wiped, photos suggest
Podesta’s iPhone reportedly wiped within hours of his Twitter account being hacked. Unconfirmed evidence builds a strong case that an Apple iCloud account belonging to Hillary Clinton’s campaign chief, JohnRead More →