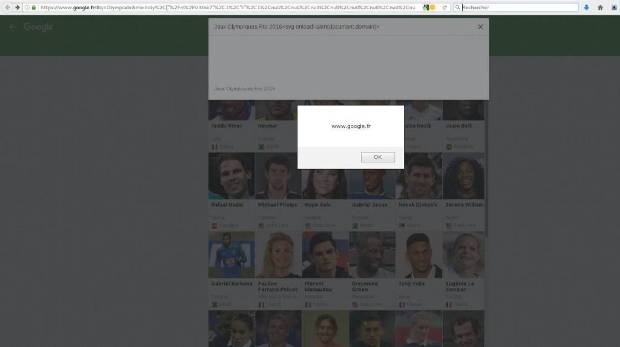
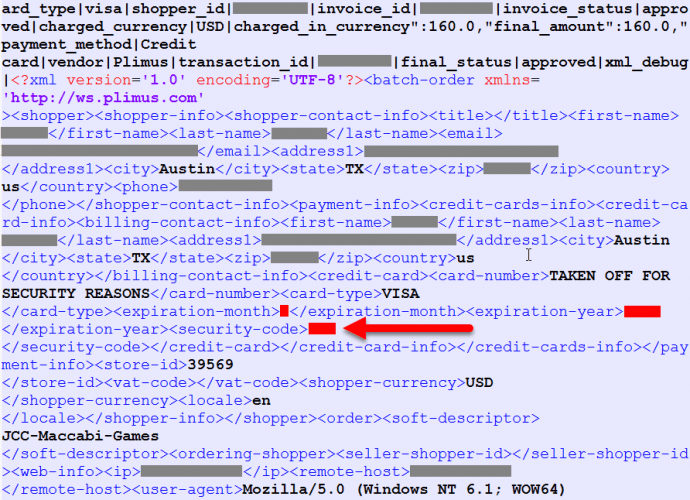
How to hack Google FR by exploiting a cross-site scripting flaw
The security expert Issam Rabhi (@issam_rabhi) has discovered a cross-site scripting vulnerability in Google France. The giant already fixed it. A security expert from French security outfit Sysdream, Issam RabhiRead More →