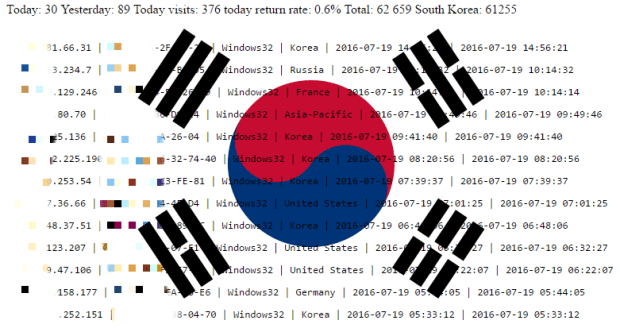
BlackMoon Banking Trojan Infected over 160,000 South Koreans
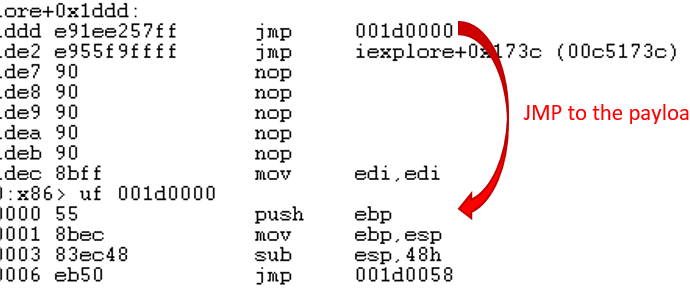
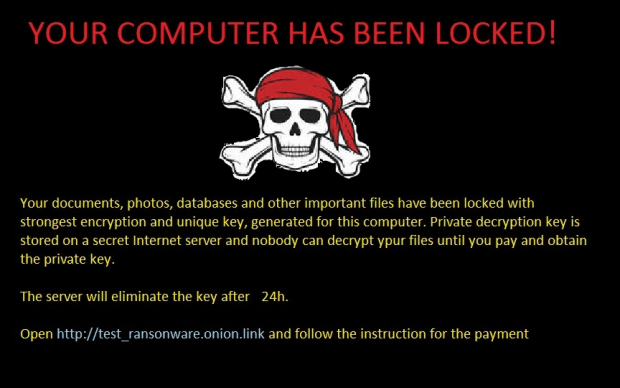
The crooks behind the recent campaign may be from China. Over 100,000 South Koreans had their banking credentials stolen by crooks who leveraged the BlackMoon banking trojan, also detected asRead More →