WinRAR and ZIP File Exploits: This ZIP File Hack Could Let Malware Bypass Your Antivirus
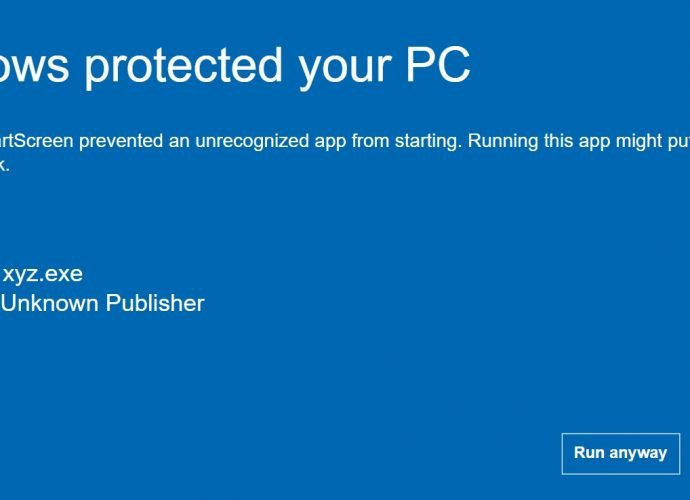
In a new cyber threat exploiting ZIP file concatenation, attackers use a Trojan embedded in concatenated ZIP files to target Windows users, evading standard detection methods. This technique takes advantageRead More →